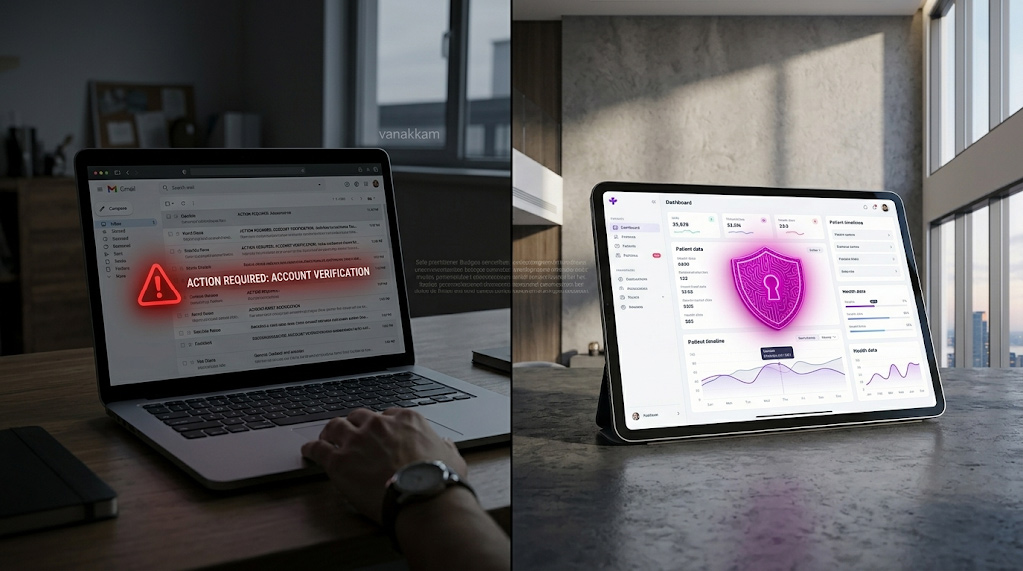
In today’s digital landscape, cybersecurity is more critical than ever. With cyber threats constantly evolving, organizations must be proactive in protecting their data and systems. This requires a comprehensive understanding of key cybersecurity functions and roles. This article will guide you through the essentials of cybersecurity, focusing on the fundamental roles and functions that are vital for maintaining robust security.
Cybersecurity isn’t just about installing antivirus software or firewalls. It’s a complex field that involves various functions working together to protect an organization’s digital assets. The National Institute of Standards and Technology (NIST) has outlined five core functions in its Cybersecurity Framework, known as the CSF functions, which provide a structured approach to managing cybersecurity risks.
Identify
The first function is to identify. This involves understanding the organization’s environment to manage cybersecurity risks effectively. It includes asset management, business environment, governance, risk assessment, and risk management strategy. By identifying what needs protection, organizations can prioritize their efforts and allocate resources efficiently.
Asset Management
Asset management involves cataloging all hardware, software, and data within the organization. Understanding what assets exist helps in evaluating their value and vulnerability. This step is crucial for setting up protective measures tailored to the organization’s specific needs.
Business Environment
Understanding the business environment involves analyzing the organizational structure and industry context. This helps in identifying potential threats and compliance requirements. By aligning cybersecurity with business objectives, organizations can ensure that security measures support operational goals.
Governance and Risk Management
Governance involves establishing policies and procedures that guide cybersecurity efforts. It includes defining roles and responsibilities and ensuring accountability. Risk management involves identifying, assessing, and prioritizing risks to minimize their impact on the organization.
Protect
Once the risks are identified, the next step is to protect. This involves implementing appropriate safeguards to ensure the delivery of critical infrastructure services. Protection measures include access control, data security, and protective technology. The goal is to limit or contain the impact of a potential cybersecurity event.
Access Control
Access control mechanisms restrict unauthorized users from accessing sensitive information. Techniques such as multi-factor authentication and role-based access control are employed to ensure that only authorized individuals have access to critical systems.
Data Security
Data security entails protecting data from unauthorized access and corruption throughout its lifecycle. Encryption, data masking, and secure data storage are essential components. These measures ensure that data remains confidential and intact, even if unauthorized access occurs.
Protective Technology
Implementing protective technology involves deploying tools and software designed to safeguard systems. Firewalls, intrusion detection systems, and antivirus programs are examples. These technologies act as the first line of defense against cyber threats.
Detect
The detect function is about identifying the occurrence of a cybersecurity event in a timely manner. It includes detection processes, continuous monitoring, and detection tools. Early detection is crucial for minimizing damage and responding effectively to threats.
Detection Processes
Detection processes involve establishing procedures for identifying potential security events. This includes defining what constitutes a threat and setting thresholds for alerts. Clear processes enable swift identification and response to incidents.
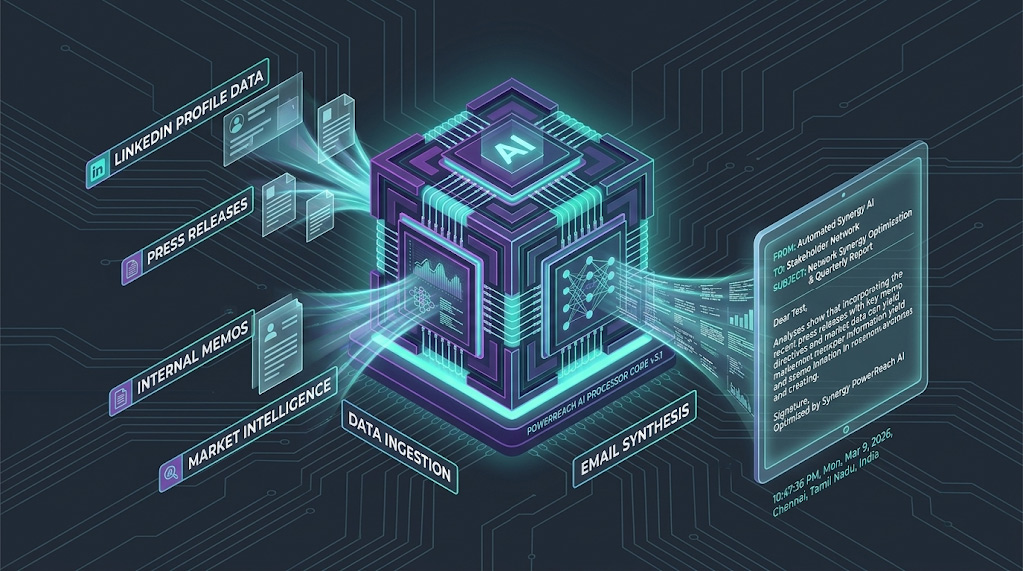
Continuous Monitoring
Continuous monitoring involves real-time surveillance of networks and systems to identify anomalies. Advanced analytics and machine learning can be used to detect unusual patterns that may indicate a breach. This proactive approach helps organizations stay ahead of emerging threats.
Detection Tools
Detection tools include software and hardware designed to identify and alert on potential threats. Security Information and Event Management (SIEM) systems aggregate and analyze data from multiple sources. These tools provide actionable insights that support rapid response efforts.
Respond
When a cybersecurity incident occurs, the respond function comes into play. This involves taking appropriate action to contain the impact of the event. Response planning, communications, analysis, mitigation, and improvements are all part of this function. An effective response can significantly reduce the consequences of a security breach.
Response Planning
Response planning involves developing and documenting procedures for handling security incidents. This includes defining roles, responsibilities, and communication channels. A well-structured plan ensures that all team members know their part in the response process.
Communication
Effective communication during a cybersecurity incident is vital for coordinating efforts and maintaining transparency. Internal and external communication strategies should be in place to inform stakeholders and manage public perception. Clear communication helps maintain trust and control the narrative.
Analysis and Mitigation
Analyzing the incident involves understanding the cause and extent of the breach. This information guides mitigation efforts aimed at containing and eradicating the threat. A thorough analysis helps prevent recurrence and informs future prevention strategies.
Recover
The final function is to recover. This involves maintaining plans for resilience and restoring any capabilities or services that were impaired due to a cybersecurity incident. Recovery planning, improvements, and communications are essential components of this function. The objective is to restore normal operations as quickly as possible and learn from the incident to improve future responses.
Recovery Planning
Recovery planning involves preparing for the restoration of services and capabilities. This includes identifying critical systems and defining priorities for recovery. Effective planning helps minimize downtime and ensures business continuity.
Continuous Improvement
Continuous improvement involves analyzing the incident and response to identify areas for enhancement. Lessons learned are integrated into policies and procedures to strengthen future responses. This iterative process helps organizations build resilience against future threats.
Recovery Communications
Communication during recovery involves updating stakeholders on the progress of restoration efforts. Keeping customers, partners, and employees informed helps maintain confidence and trust. Transparent communication is key to managing expectations and supporting recovery efforts.
Key Cybersecurity Roles
To effectively implement these functions, organizations need skilled professionals in various cybersecurity roles. Each role plays a crucial part in protecting digital assets and ensuring compliance with security protocols.
Chief Information Security Officer (CISO)
The CISO is responsible for developing and implementing an information security program, which includes procedures and policies designed to protect enterprise communications, systems, and assets from both internal and external threats. The CISO ensures that the organization’s cybersecurity strategy aligns with its business goals and complies with regulatory requirements.
Strategic Leadership
The CISO provides strategic leadership in developing cybersecurity initiatives. They align security strategies with business objectives, ensuring that security measures support overall goals. This role requires a deep understanding of both technology and business operations.
Policy Development
Policy development involves creating comprehensive security policies and procedures. The CISO oversees the formulation and implementation of guidelines that govern security practices. These policies provide a framework for consistent and effective security measures across the organization.
Regulatory Compliance
The CISO ensures that the organization complies with relevant laws and regulations. This involves staying informed about changes in the regulatory landscape and adjusting security practices accordingly. Compliance is crucial for avoiding legal penalties and maintaining industry standards.
Security Operations Center (SOC) Analyst
A SOC Analyst monitors an organization’s network and systems for malicious activity. They use various tools to detect threats and respond to incidents. SOC Analysts are on the front lines of threat management and play a critical role in maintaining network security.
Threat Detection
Threat detection involves identifying potential security incidents using specialized tools and techniques. SOC Analysts monitor network traffic and system logs for signs of malicious activity. Early detection enables rapid response and minimizes the impact of threats.
Incident Response
SOC Analysts play a key role in incident response efforts. They collaborate with other security professionals to contain and mitigate incidents. This involves executing predefined response plans and coordinating efforts to restore normal operations.
Continuous Monitoring
Continuous monitoring is a fundamental responsibility of SOC Analysts. They use advanced monitoring tools to maintain real-time surveillance of network activity. This proactive approach helps identify and address threats before they escalate into significant incidents.
Risk Assessment Specialist
Risk Assessment Specialists identify and evaluate potential risks that could affect an organization’s operations. They conduct risk assessments and develop strategies to mitigate risks. Their work ensures that the organization understands its vulnerabilities and takes proactive measures to address them.
Risk Identification
Risk identification involves recognizing potential threats and vulnerabilities within the organization. Risk Assessment Specialists analyze the organization’s assets, processes, and environment to identify areas of concern. This step is crucial for prioritizing risk management efforts.
Risk Evaluation
Risk evaluation involves assessing the likelihood and impact of identified risks. Specialists use various methods to quantify risks and determine their significance. This evaluation informs the development of strategies to mitigate or manage risks.
Mitigation Strategies
Mitigation strategies involve developing plans to reduce or eliminate risks. Specialists collaborate with other departments to implement measures that address identified vulnerabilities. Effective strategies help minimize the potential impact of risks on the organization.
Incident Response Coordinator
Incident Response Coordinators manage the response to security incidents. They coordinate with different departments to ensure a swift and effective response. This role is vital for minimizing the impact of security breaches and restoring normal operations.
Coordination
Coordination involves orchestrating efforts across various teams during a security incident. Incident Response Coordinators ensure that all stakeholders are informed and aligned in their response efforts. Effective coordination is key to a unified and efficient response.
Communication
Communication is a critical aspect of incident response management. Coordinators facilitate communication between internal teams and external parties, such as law enforcement or regulatory bodies. Clear communication channels help streamline response efforts and minimize confusion.
Documentation and Analysis
Documentation and analysis involve recording details of the incident and response efforts. Coordinators document actions taken, decisions made, and outcomes achieved. This information is crucial for post-incident analysis and continuous improvement efforts.
Vulnerability Management Specialist
A Vulnerability Management Specialist identifies, evaluates, and mitigates vulnerabilities in an organization’s systems. They conduct regular scans and assessments to ensure that vulnerabilities are addressed before they can be exploited by attackers.
Vulnerability Scanning
Vulnerability scanning involves using specialized tools to identify weaknesses in systems and applications. Specialists conduct regular scans to detect new vulnerabilities and assess their potential impact. This proactive approach helps prevent exploitation by attackers.
Evaluation and Prioritization
Evaluation and prioritization involve assessing the severity of identified vulnerabilities. Specialists determine the potential impact on the organization and prioritize remediation efforts accordingly. This ensures that critical vulnerabilities are addressed promptly.
Remediation and Mitigation
Remediation and mitigation involve developing and implementing solutions to address vulnerabilities. Specialists collaborate with IT and security teams to apply patches, configure systems, and deploy protective measures. These efforts help strengthen the organization’s security posture.
Compliance Officer
Compliance Officers ensure that the organization adheres to relevant laws, regulations, and standards related to cybersecurity. They develop compliance measures and conduct audits to ensure that the organization meets its legal obligations.
Regulatory Awareness
Regulatory awareness involves staying informed about changes in laws and regulations affecting cybersecurity. Compliance Officers monitor regulatory developments and adjust the organization’s practices accordingly. This helps ensure ongoing compliance and avoid legal penalties.
Compliance Audits
Compliance audits involve evaluating the organization’s adherence to established standards and regulations. Officers conduct regular audits to identify gaps and recommend corrective actions. These audits provide assurance that the organization meets its legal and regulatory obligations.
Policy Implementation
Policy implementation involves developing and enforcing compliance-related policies and procedures. Compliance Officers work with other departments to integrate these policies into daily operations. This ensures consistent adherence to legal and regulatory requirements.
Implementing Security Protocols and Compliance Measures
by Markus Winkler (https://unsplash.com/@markuswinkler)
Implementing security protocols and compliance measures is essential for protecting data and ensuring regulatory compliance. Here are some key strategies:
Develop Strong Security Policies
Organizations should develop comprehensive security policies that outline procedures for protecting data and systems. These policies should cover areas such as access control, data protection, and incident response.
Policy Formulation
Policy formulation involves creating detailed guidelines that govern security practices. Organizations should define clear roles, responsibilities, and procedures for managing security. Comprehensive policies provide a framework for consistent and effective security measures.
Policy Enforcement
Policy enforcement involves ensuring adherence to established security policies. Organizations should implement monitoring and auditing processes to verify compliance. Enforcement mechanisms help maintain accountability and prevent lapses in security practices.
Policy Review and Updates
Policy review and updates involve regularly assessing and revising security policies. Organizations should adapt policies to reflect changes in the threat landscape, technology, and regulations. Regular updates ensure that policies remain relevant and effective.
Conduct Regular Risk Assessments
Regular risk assessments help organizations identify potential vulnerabilities and take proactive measures to address them. This involves evaluating the effectiveness of existing controls and implementing new measures where necessary.
Assessment Planning
Assessment planning involves defining the scope and objectives of risk assessments. Organizations should identify the assets, processes, and areas to be evaluated. Clear planning ensures that assessments are comprehensive and aligned with organizational goals.
Risk Evaluation Methods
Risk evaluation methods involve using qualitative and quantitative techniques to assess risks. Organizations should apply appropriate methodologies to determine the likelihood and impact of identified risks. This evaluation guides the development of mitigation strategies.
Mitigation Implementation
Mitigation implementation involves executing strategies to address identified risks. Organizations should collaborate with relevant departments to apply controls and safeguards. Effective implementation helps reduce the potential impact of risks on operations.
Implement Continuous Monitoring
Continuous monitoring is critical for detecting threats in real time. Organizations should use advanced monitoring tools to track network activity and identify anomalies that could indicate a security breach.
Monitoring Tools
Monitoring tools include software and hardware solutions that enable real-time surveillance of systems and networks. Organizations should deploy tools that provide comprehensive visibility and alert capabilities. These tools support proactive threat detection and response.
Anomaly Detection
Anomaly detection involves identifying deviations from normal activity patterns. Organizations should use machine learning and analytics to detect unusual behaviors that may indicate a security breach. Early detection helps prevent incidents from escalating.
Response Integration
Response integration involves linking monitoring efforts with incident response processes. Organizations should ensure that alerts trigger predefined response actions. This integration ensures a swift and coordinated response to detected threats.
Ensure Regulatory Compliance
Compliance with relevant laws and regulations is essential for avoiding legal penalties and protecting an organization’s reputation. Organizations should stay informed about changes in regulations and ensure that their security practices meet the required standards.
Regulatory Monitoring
Regulatory monitoring involves tracking changes in laws and standards affecting cybersecurity. Organizations should assign responsibilities for staying informed about regulatory developments. This monitoring helps ensure ongoing compliance and proactive adjustments.
Compliance Frameworks
Compliance frameworks provide structured approaches for meeting regulatory requirements. Organizations should adopt frameworks such as ISO 27001 or GDPR to guide their compliance efforts. These frameworks offer best practices and standards for effective cybersecurity management.
Compliance Training
Compliance training involves educating employees about relevant laws and regulations. Organizations should conduct regular training sessions to raise awareness and ensure understanding of compliance obligations. Informed employees are critical for maintaining adherence to legal standards.
Conclusion
Understanding key cybersecurity functions and roles is essential for protecting an organization’s digital assets. By implementing the core functions outlined in the NIST Cybersecurity Framework and employing skilled professionals in critical roles, organizations can effectively manage cybersecurity risks. Additionally, implementing strong security protocols and compliance measures ensures that organizations are prepared to respond to threats and maintain resilience in the face of cyber attacks.
By staying informed and proactive, organizations can create a robust security posture that protects their data and systems from evolving cyber threats. Through continuous improvement and strategic planning, organizations can build resilience and trust in their security practices, ensuring long-term success in a digital world.