Understanding HIPAA regulations is crucial for anyone in the healthcare industry. These regulations protect patient information and ensure privacy.
HIPAA stands for the Health Insurance Portability and Accountability Act. It was enacted in 1996 to safeguard health data.
The primary purpose of HIPAA is to protect patient privacy. It also aims to prevent healthcare fraud and abuse.
HIPAA compliance is mandatory for healthcare providers and related entities. It involves adhering to specific rules and standards.
Protected Health Information (PHI) is a key concept in HIPAA. PHI includes any data that can identify a patient.
The HIPAA Privacy Rule regulates the use and disclosure of PHI. It ensures that patient information is handled with care.
The Security Rule under HIPAA sets standards for electronic PHI protection. It requires implementing safeguards to secure data.
Understanding these regulations is essential for maintaining patient trust and avoiding legal penalties.
What is HIPAA? Definition, Purpose, and History
HIPAA, or the Health Insurance Portability and Accountability Act, was introduced in 1996. It was created to safeguard patient health information. The act plays a key role in the healthcare field today.
The purpose of HIPAA is multifaceted. It aims to protect sensitive patient data and streamline healthcare processes. It also seeks to combat fraud and ensure data privacy.
HIPAA ensures that patient information remains confidential and secure. This is critical to building trust between patients and healthcare providers. The law provides a framework for managing health data.
Key provisions of HIPAA include:
- Protecting patient rights and confidentiality
- Ensuring data privacy and security
- Establishing national standards for electronic health care transactions
Since its inception, HIPAA has undergone various updates. These changes address evolving technology and data challenges. Despite challenges, HIPAA remains crucial in maintaining health data standards.
Understanding HIPAA is vital for healthcare stakeholders. It helps ensure compliance and protect sensitive patient information from unauthorized access.
The Five Main Components of HIPAA
HIPAA is built upon five main components that ensure comprehensive protection and standardization within healthcare.
These components create a robust framework for privacy, security, and compliance.
Understanding each component is essential for healthcare organizations and professionals.
The five key components include:
- Privacy Rule
- Security Rule
- Transactions and Code Sets Rule
- Unique Identifiers Rule
- Enforcement Rule
Each component serves a specific purpose within the broader HIPAA framework.
They collectively safeguard patient information and ensure data integrity. Compliance with these components is crucial for legal and ethical responsibilities in healthcare.
Familiarity with these elements aids in maintaining secure and efficient health care operations.
1. HIPAA Privacy Rule
The HIPAA Privacy Rule sets the standard for protecting patient health information. It governs how healthcare entities handle PHI. This rule aims to keep patient information private and secure.
The Privacy Rule applies to all forms of PHI, whether written, electronic, or spoken. It allows patients to understand and control how their information is used. This fosters trust between patients and healthcare providers.
Key provisions of the Privacy Rule include:
- Patients’ right to access their medical records
- Limits on the use and sharing of information
- Requirements for confidentiality agreements
Healthcare providers must inform patients about their privacy rights. They should also notify how their information is used or shared. Failure to adhere could result in penalties.
Regular training helps employees understand and comply with the Privacy Rule. This ensures that they handle patient information responsibly. A commitment to privacy is essential for compliance.
The Privacy Rule balances protecting patient rights with ensuring necessary information flow. This enables high-quality healthcare delivery while respecting patient confidentiality.
2. HIPAA Security Rule
The HIPAA Security Rule specifically protects electronic PHI (ePHI). It sets standards for safeguarding ePHI through various means. This rule mandates administrative, physical, and technical safeguards.
The Security Rule requires risk assessments to pinpoint vulnerabilities. These assessments help healthcare entities strengthen their data protection strategies. Security measures must align with the identified risks.
Key elements of the Security Rule include:
- Administrative safeguards such as policies and procedures
- Physical safeguards like secure facilities
- Technical safeguards including encryption and access controls
Organizations must ensure employees receive adequate security training. This helps them recognize potential threats and avoid breaches. Security is a shared responsibility among all staff.
Conducting regular audits is crucial to maintain compliance with the Security Rule. Audits allow organizations to uncover areas needing improvement. Staying vigilant is essential to secure patient data.
The Security Rule enables healthcare providers to effectively protect sensitive data. Robust security practices reduce the risk of unauthorized access. This ensures patients’ trust in the healthcare system.
3. HIPAA Transactions and Code Sets Rule
The HIPAA Transactions and Code Sets Rule standardizes electronic health transactions. It ensures these transactions adhere to consistent formats. This simplifies data exchange and processing.
Uniformity across transactions reduces administrative burdens. It also improves accuracy in data handling and reimbursement processes. Standardization benefits both healthcare providers and payers.
Key provisions include:
- Standardized transaction code sets
- Rules for electronic data interchange
- Enhancements in billing and claims processes
This rule supports efficient operations and accurate healthcare transactions. By reducing variability, it enables smoother communication between systems. This ultimately benefits patient care coordination.
4. HIPAA Unique Identifiers Rule
The HIPAA Unique Identifiers Rule mandates standardized identifiers for entities. These identifiers streamline healthcare transactions. They improve efficiency and reduce administrative overhead.
Unique identifiers ensure that each entity in the healthcare ecosystem is clearly identifiable. This clarity is crucial for accurate billing and data exchange.
Key identifiers include:
- National Provider Identifier (NPI)
- Employer Identification Number (EIN)
- Health Plan Identifier (HPID)
These identifiers facilitate seamless communication among healthcare entities. They help maintain consistency and integrity in health data. Such clarity improves operational efficiency and reduces errors.
5. HIPAA Enforcement Rule
The HIPAA Enforcement Rule establishes procedures for investigating and penalizing non-compliance. It ensures that healthcare entities are held accountable. This rule underscores the importance of compliance.
The Enforcement Rule details the consequences of HIPAA violations. It outlines tiered penalties based on the severity of non-compliance. Penalties aim to deter negligence and encourage diligence.
Key elements include:
- Guidelines for investigations and compliance reviews
- Determination of penalty severity and tier
- Methods for resolution and corrective action
The Enforcement Rule underscores the importance of proactive compliance. It reminds healthcare entities of their legal obligations. Organizations must invest in compliance to avoid severe penalties and maintain trust.
What is Protected Health Information (PHI)?
Protected Health Information (PHI) refers to any data that can identify a patient. This includes medical records and personal details associated with healthcare services.
PHI is crucial in the healthcare industry due to its sensitive nature. It covers a broad range of information.
PHI under HIPAA includes:
- Names and addresses
- Social Security numbers
- Medical records and conditions
- Treatment histories
- Health insurance details
The HIPAA Privacy and Security Rules safeguard PHI. These rules restrict its use and disclosure to protect patient privacy. Maintaining PHI security is paramount in healthcare.
Compliance with HIPAA ensures that PHI is handled with confidentiality. Regular updates to privacy policies help in managing PHI effectively. This maintains the trust of patients in the healthcare system.
Understanding PHI is essential for healthcare providers and administrators. It helps them implement strategies to protect patient data. Effective PHI management is key to achieving compliance.
PHI in Medical Terms: What Does It Include?
In medical terms, PHI encompasses all information relating to a patient’s health status. This includes demographics linked to healthcare services.
PHI can be found in various formats, such as paper, electronic, or spoken. It is critical to protect these details against unauthorized access.
Components of PHI include:
- Lab test results
- Appointment notes
- Prescription information
Managing PHI requires robust security measures and regular staff training. Understanding the scope of PHI helps healthcare providers safeguard patient privacy effectively.
Individually Identifiable Information Under HIPAA
Individually Identifiable Information is any data that can distinguish one person. Under HIPAA, this is part of the PHI.
Such information requires strict handling to prevent breaches. A thoughtful approach protects patients’ rights.
Examples of Individually Identifiable Information:
- Names
- Birthdates
- Email addresses
Ensuring security for this information is a top priority. Effective strategies and compliance with HIPAA rules are necessary for protecting this sensitive information.
Who Must Comply with HIPAA?
HIPAA compliance is required for specific categories in the healthcare sector. These entities are bound by law to follow HIPAA guidelines to ensure data protection.
Primarily, HIPAA applies to:
- Healthcare providers: doctors, clinics, hospitals
- Health plans: insurance companies, HMOs
- Healthcare clearinghouses: process nonstandard data
Additionally, business associates that handle PHI on behalf of covered entities must also comply. This includes contractors providing services like billing or data analysis.
Compliance is crucial in maintaining trust and legal standing. It ensures that all parties protect the sensitive health data of individuals.
Covered Entities and Business Associates
Covered entities include healthcare providers who transmit health data electronically. They play a direct role in patient care and data handling.
Business associates are individuals or entities providing services to covered entities. These services often involve access to PHI.
Examples of business associates:
- Third-party billing companies
- IT service providers
- Legal consultants
Both groups must adhere to HIPAA rules. Their collaboration is essential in safeguarding health information. Regular assessments ensure ongoing compliance and data protection.
HIPAA Compliance Requirements: Key Obligations
HIPAA compliance requires adhering to established protocols to protect patient information. This involves several critical obligations for covered entities and business associates. Meeting these requirements is not just about avoiding penalties but ensuring trustworthiness.
Compliance obligations include:
- Developing and maintaining written policies
- Regular employee training on privacy and security
- Conducting risk assessments and audits
Written policies and procedures form the backbone of HIPAA compliance. They provide a framework for handling PHI securely and consistently.
Training programs keep employees informed about the latest regulations and security practices. Awareness is a crucial defense against data breaches.
Risk assessments identify vulnerabilities within the organization. They help implement effective safeguards and improvements. Regular audits ensure ongoing compliance and identify areas needing improvement.
HIPAA compliance is a dynamic process, requiring constant vigilance. It involves adapting to regulatory changes and technological advancements. Commitment to compliance results in better data security and improved patient trust.
Written Policies and Procedures
Written policies outline how an organization handles PHI. They should be clear, accessible, and comprehensive. These documents guide daily operations and decision-making.
Policies should cover:
- Data access controls
- Breach response plans
They ensure consistency in handling health information. Regular updates reflect changes in regulations or organizational practices.
Employee Training and Awareness
Training programs prepare staff for compliant data handling. Regular sessions help maintain up-to-date knowledge. Awareness activities emphasize the importance of privacy and security.
Key training topics include:
- PHI handling procedures
- Recognizing and reporting breaches
Well-informed employees are a first line of defense against potential risks. Ongoing education is vital to an effective security culture.
Risk Assessments and Audits
Risk assessments evaluate potential threats to PHI security. They help identify vulnerabilities and areas needing improvement. Assessments guide the development of robust security measures.
Focus areas include:
- Identifying weak access points
- Evaluating current safeguards
Regular audits verify compliance with HIPAA requirements. They also provide insights into needed policy or procedural changes. Proactive assessments and audits bolster PHI protection.
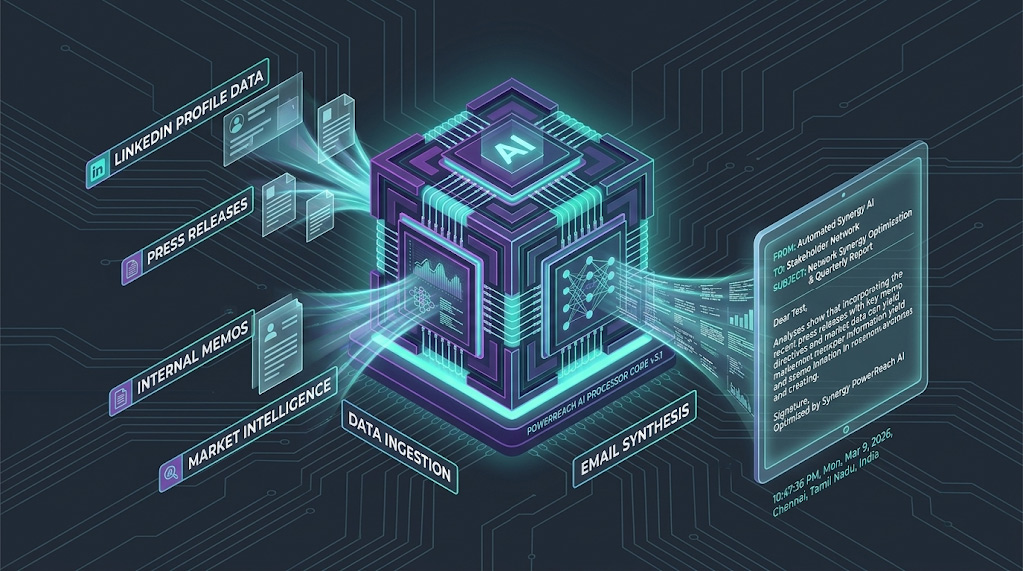
HIPAA Security Rule: Safeguarding Electronic PHI
The HIPAA Security Rule establishes standards for protecting electronic Protected Health Information (ePHI). Its goal is to maintain data confidentiality, integrity, and availability.
Organizations must implement comprehensive safeguards. These measures prevent unauthorized access and ensure data protection.
Key elements of the Security Rule involve:
- Administrative safeguards
- Physical safeguards
- Technical safeguards

Failure to apply these measures can lead to significant consequences. Protecting electronic health information is crucial in today’s digital age. Organizations must continuously update and adapt their security measures.
Administrative, Physical, and Technical Safeguards
Administrative safeguards establish policies for managing ePHI security. They outline procedures and designate responsible personnel.
Key areas include:
- Security management processes
- Workforce training programs
Physical safeguards protect the infrastructure housing ePHI. They involve securing facilities and equipment.
Focus areas include:
- Access controls to physical locations
- Protection against environmental hazards
Technical safeguards involve technology solutions for ePHI protection. They focus on access control and information security.
Important elements include:
- Implementing encryption
- Monitoring data access
Encryption, Access Controls, and Data Security
Encryption is a critical security tool. It protects ePHI during transmission and storage. By encrypting data, organizations safeguard it against unauthorized access.
Access controls ensure that only authorized individuals can view ePHI. They restrict data access based on roles and responsibilities.
Key components include:
- User authentication mechanisms
- Role-based access permissions
Data security involves ongoing monitoring and risk management. It addresses vulnerabilities and enhances defenses.
Important strategies include:
- Conducting regular security evaluations
- Implementing robust incident response plans
Focusing on these areas strengthens the security of electronic health information. It helps comply with HIPAA regulations while maintaining patient trust.
HIPAA Privacy Rule: Use and Disclosure of PHI
The HIPAA Privacy Rule sets strict standards for handling Protected Health Information (PHI). It governs how PHI can be used and disclosed. The rule aims to protect patient privacy while allowing necessary data flow.
Covered entities must adhere to these regulations. They are required to implement policies ensuring compliance. The rule provides patients with rights over their health information.
Key aspects of the Privacy Rule include:
- Defining who may access PHI
- Establishing boundaries for data use
- Providing patients with access rights
Ensuring compliance helps build patient trust and maintain data integrity. Organizations must stay updated on rule provisions.
Minimum Necessary Standard and Patient Rights
The “Minimum Necessary” standard limits PHI use. It requires sharing only the information needed for a specific purpose. This approach minimizes exposure risks.
Patients gain several rights under the Privacy Rule. They can access and request corrections to their health information.
Key patient rights include:
- Receiving information disclosures
- Requesting access to personal medical records
Understanding and implementing these standards is vital. Organizations must respect patient rights to maintain trust.
Permitted Uses and Disclosures
The HIPAA Privacy Rule outlines specific scenarios where PHI use and disclosure are permitted. Organizations may share data without patient consent in certain cases.
Permitted situations include:
- Treatment, payment, and healthcare operations
- Disclosures required by law
It’s crucial to know these scenarios to ensure compliant practices. Understanding them avoids potential violations and penalties.
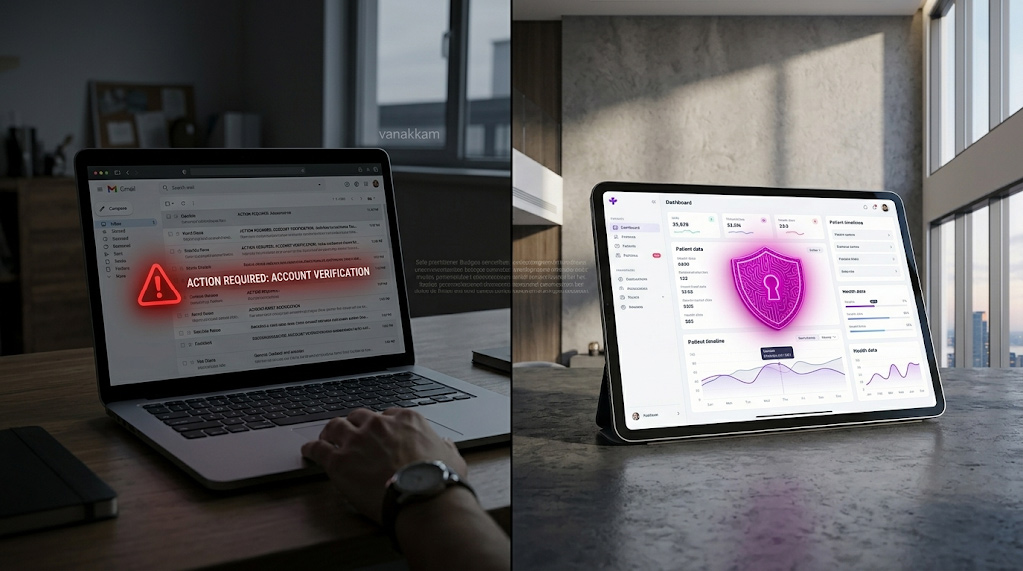
HIPAA Breach Notification Rule: Responding to Incidents
When a data breach occurs, swift action is crucial. The HIPAA Breach Notification Rule outlines how organizations must respond to breaches of Protected Health Information (PHI). This rule ensures affected individuals are informed promptly.
Prompt notification is not only a requirement but also a step towards transparency. It maintains trust with patients and authorities. Organizations must have a clear plan for responding to breaches.
Core breach response actions include:
- Identifying and assessing the breach
- Notifying affected individuals
- Reporting to the Department of Health and Human Services (HHS)
Preparedness in handling breaches can mitigate negative impacts. It also enhances overall data protection efforts.
Breach Notification Requirements and Timelines
Specific criteria govern breach notifications. The law mandates that notifications are issued without unreasonable delay. Typically, within 60 days of discovery. Timely communication is vital for trust.
Notifications must include key details such as:
- Description of the breach
- Steps individuals should take
- Measures taken to protect further exposure
Adhering to these timelines and requirements is essential. It ensures compliance and aids in maintaining patient trust.
Preventing Fraud and Abuse: HIPAA Provisions
HIPAA includes specific provisions to combat fraud and abuse in healthcare. These rules are crucial for maintaining the system’s integrity. They focus on ensuring transparency and accountability among healthcare providers.
Key provisions that help prevent fraud and abuse include:
- Implementing effective compliance programs
- Conducting regular audits and monitoring
- Establishing clear reporting mechanisms for suspicious activities
Enforcing these provisions can significantly reduce fraudulent activities. It also encourages ethical practices within the healthcare sector. Regular checks and balances are essential for safeguarding both patient rights and public funds.
Common HIPAA Violations and How to Avoid Them
Understanding common HIPAA violations is crucial for healthcare providers. These errors can lead to severe penalties. Most violations occur due to negligence or ignorance.
Some typical HIPAA violations include:
- Unauthorized access to PHI
- Improper disposal of PHI
- Failure to encrypt sensitive data
- Lack of employee training on HIPAA regulations
Avoiding these violations involves implementing robust security measures. Regular employee training is essential. Train staff to understand HIPAA’s importance and their role in compliance.
Proactive steps can help prevent data breaches. Compliance ensures protection for patients and avoids hefty fines. Regular reviews of policies and systems also contribute to ongoing compliance.
Enforcement, Penalties, and Real-World Examples
The enforcement of HIPAA is carried out by the Office for Civil Rights (OCR). They investigate complaints and conduct compliance audits. Their role is crucial in maintaining adherence to regulations.
Non-compliance can lead to significant penalties. Fines range based on the severity of the violation. Entities might face fines from $100 to $50,000 per violation. In extreme cases, this can total millions.
Real-world examples highlight the importance of compliance:
- A major healthcare provider faced a $16 million penalty for data breaches.
- Smaller practices also received fines for improper PHI disposal.
- Data loss due to unencrypted devices led to substantial financial repercussions.
Lessons from these examples emphasize the need for diligent adherence. Entities must regularly update practices and conduct risk assessments. Understanding enforcement and penalties can inspire proactive compliance.
Best Practices for HIPAA Compliance
Ensuring compliance with HIPAA involves adopting effective strategies. Entities should establish a robust framework. This strengthens adherence to regulations and protects patient information.
Key practices include:
- Implementing comprehensive risk assessments regularly.
- Conducting routine staff training focused on privacy policies.
- Utilizing advanced encryption methods for sensitive data.
- Setting up strict access controls to manage PHI security.
Organizations should maintain updated policies and procedures. Continuous monitoring is crucial to identify potential vulnerabilities. Proactively addressing these can prevent violations.
Regular audits help verify compliance measures’ effectiveness. These audits uncover areas needing improvement. By following these best practices, entities can significantly enhance their HIPAA compliance efforts.
Recent Updates and Future Trends in HIPAA
HIPAA continues to evolve to address modern challenges. Recent updates focus on improving data security. This reflects the growing importance of protecting digital health records.
Emerging trends highlight:
- Increased emphasis on cybersecurity measures.
- Adoption of advanced technology for stronger compliance.
- Greater enforcement of penalties for breaches.
Staying informed about these changes is crucial. Organizations must adapt to remain compliant. This ensures they are prepared for future regulatory advancements.
Conclusion: The Importance of HIPAA Compliance
HIPAA compliance is essential for safeguarding patient information. It protects privacy while ensuring data security and confidentiality.
Non-compliance can lead to severe penalties and loss of trust. Adhering to HIPAA not only meets legal obligations but strengthens patient relationships. Through diligence and awareness, organizations can continue providing safe healthcare services.