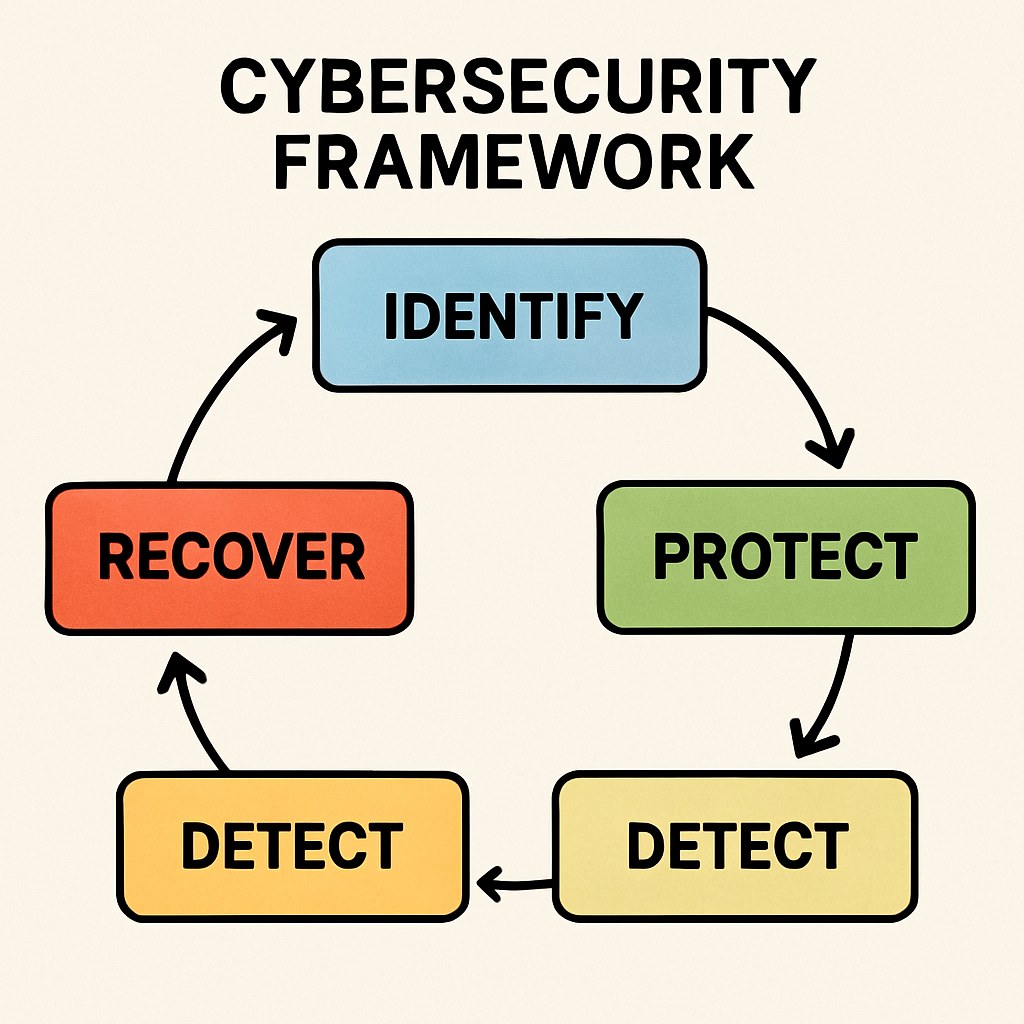
Before diving into the specifics, it’s essential to understand what a cybersecurity framework entails. Essentially, it is a structured approach to managing and mitigating risks associated with digital information and infrastructure.
A cybersecurity framework acts as a blueprint for securing digital assets. It involves protocols and procedures designed to protect data integrity, confidentiality, and availability. Understanding its components is crucial for effective implementation.
The core components typically include risk management processes, security controls, and compliance measures. Each element plays a pivotal role in ensuring that the framework is robust and adaptable to emerging threats.
Implementing a cybersecurity framework offers numerous advantages. It helps streamline security efforts, reduces the risk of breaches, and builds a security-first culture within the organization. Furthermore, it fosters trust with clients and partners by demonstrating a commitment to protecting sensitive information.
A cybersecurity framework provides a systematic approach to safeguarding data and systems. It helps organizations to:
A well-designed framework aids in the identification and analysis of potential threats. By understanding the types of threats your organization may face, you can develop targeted strategies to mitigate them.
The framework guides the implementation of security measures and policies, ensuring they are both effective and sustainable. This involves deploying the right mix of technology and processes to create a resilient security posture.
With an increasing number of regulations governing data protection, a cybersecurity framework helps ensure compliance. This not only avoids legal penalties but also enhances the organization’s reputation by demonstrating adherence to industry standards.
The first step in developing a cybersecurity framework is conducting a thorough threat assessment. This involves identifying potential threats and vulnerabilities within your network.

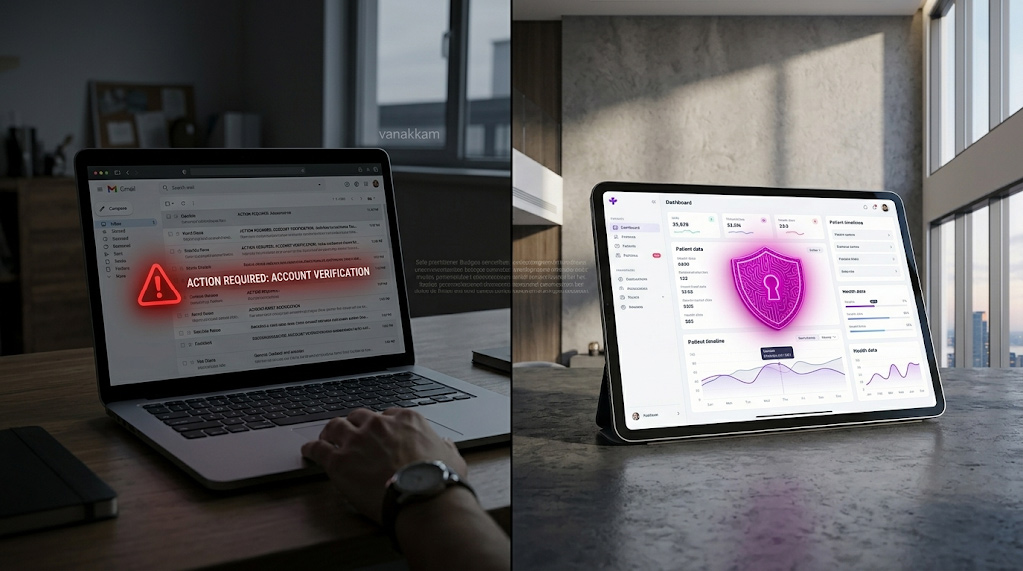
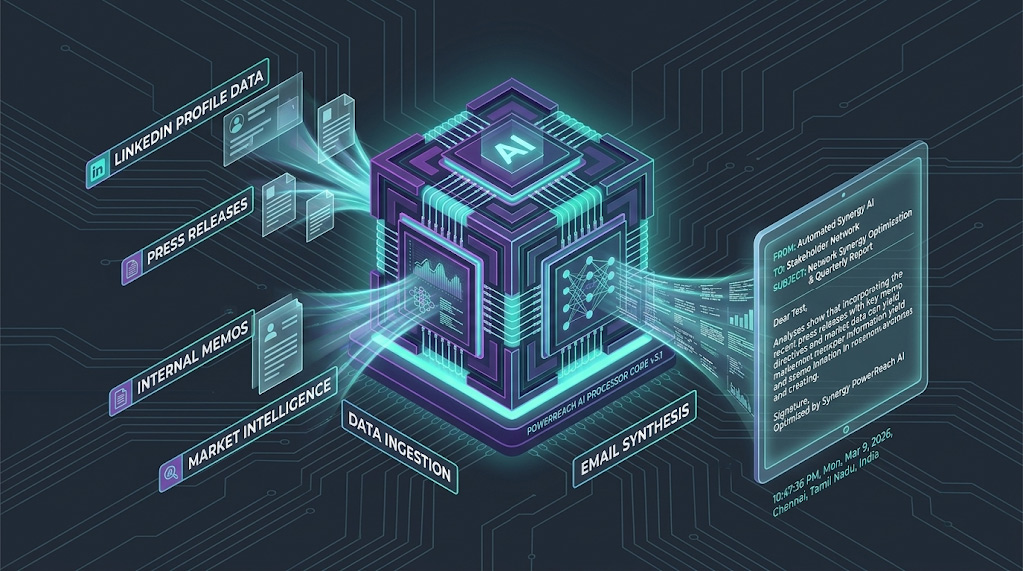
Begin by listing all possible threats, such as malware, phishing attacks, and insider threats. Understand the likelihood and impact of each threat on your organization.
- Malware Threats: Analyze the various types of malware that could infiltrate your systems, including viruses, worms, and ransomware. Understand their behavior and potential damage.
- Phishing and Social Engineering: Recognize the methods used by attackers to deceive employees into divulging sensitive information. Train staff to identify and report suspicious activities.
- Insider Threats: Evaluate the risk posed by employees or partners who have access to sensitive data. Implement policies to monitor and manage internal threats effectively.
Evaluate your current security measures to identify any weaknesses. This might involve scanning your systems for vulnerabilities and reviewing access controls.
- System Vulnerabilities: Conduct regular vulnerability scans to detect and address weaknesses in your IT infrastructure. Stay updated with patches and updates to mitigate risks.
- Access Control Weaknesses: Review and refine access controls to ensure only authorized personnel have access to critical systems. Implement multi-factor authentication for added security.
- Physical Security Gaps: Don’t overlook physical security. Ensure that data centers and critical infrastructure are protected against unauthorized physical access.
Once you’ve identified potential threats and vulnerabilities, the next step is to analyze and manage these risks.
Not all risks are equal. Prioritize them based on their potential impact and likelihood. This helps in allocating resources efficiently to address the most critical threats.
- Impact Assessment: Determine the potential impact of each identified risk on your organization’s operations, reputation, and financial standing. Classify them as high, medium, or low impact.
- Likelihood Evaluation: Evaluate the probability of each risk materializing. Consider historical data, industry trends, and expert insights to make informed assessments.
- Resource Allocation: Allocate resources strategically to address high-priority risks first. This ensures that the most significant threats are mitigated efficiently.
Develop strategies to mitigate risks. This may include technical solutions like firewalls and encryption, as well as procedural measures such as regular audits and employee training.
- Technical Solutions: Deploy advanced technical solutions, including intrusion detection systems, anti-malware software, and robust firewalls, to protect against cyber threats.
- Procedural Measures: Establish and enforce procedures such as regular security audits and compliance checks. This helps in maintaining security standards across the organization.
- Training and Awareness Programs: Implement ongoing training programs to educate employees about cybersecurity best practices. This empowers them to act as the first line of defense against cyber threats.
Security policies are the backbone of a cybersecurity framework. They define how an organization protects its information assets.
Policies should cover all aspects of security, including data protection, access controls, and incident response. They should be clear, concise, and enforceable.
- Data Protection Policies: Develop policies that specify how data should be handled, stored, and transmitted to protect its confidentiality and integrity.
- Access Control Policies: Define who has access to what information and under what circumstances. Implement strict access control measures to prevent unauthorized data access.
- Incident Response Policies: Establish protocols for responding to security incidents. This includes roles and responsibilities, communication strategies, and post-incident analysis.
It’s crucial to ensure that all employees understand and follow security policies. Regular training sessions and compliance checks can help in maintaining adherence.
- Employee Training Programs: Conduct regular training sessions to educate employees about the importance of compliance and their role in maintaining security.
- Compliance Audits: Implement periodic compliance audits to ensure that security policies are being followed. Address any non-compliance issues promptly to maintain a secure environment.
- Feedback Mechanisms: Establish feedback mechanisms to gather input from employees on the effectiveness of security policies. Use this information to make necessary adjustments.
A cyber defense plan outlines the specific steps your organization will take to protect against cyber threats.
Ensure your network is secure by using firewalls, intrusion detection systems, and secure configurations. Regularly update all systems to protect against known vulnerabilities.
- Firewall Deployment: Install and configure firewalls to monitor and control incoming and outgoing network traffic based on predetermined security rules.
- Intrusion Detection Systems: Utilize intrusion detection systems to identify and respond to potential security breaches in real-time. This helps in preventing unauthorized access.
- System Updates and Patches: Regularly update all systems and software to patch known vulnerabilities. This reduces the risk of exploitation by cyber attackers.
Implement data encryption and backup solutions to safeguard sensitive information. Ensure that access to data is restricted to authorized personnel only.
- Data Encryption: Use encryption technologies to protect sensitive data both at rest and in transit. This ensures data confidentiality, even if it is intercepted.
- Backup Solutions: Implement robust data backup solutions to ensure data availability and integrity. Regularly test backup and recovery processes to ensure they function effectively.
- Access Restrictions: Implement strict access restrictions to sensitive data. Ensure that only authorized personnel have access, and monitor access logs for suspicious activities.
An incident response plan is crucial for minimizing damage in the event of a security breach.
Prepare your team by conducting regular drills and simulations. This helps in ensuring that everyone knows their role during an actual incident.
- Simulated Drills: Conduct simulated drills to test the effectiveness of your incident response plan. This helps identify gaps and areas for improvement.
- Role Assignments: Clearly define roles and responsibilities for each team member in the event of an incident. Ensure everyone understands their role and is prepared to act.
- Communication Protocols: Establish communication protocols to ensure timely and accurate information sharing during an incident. This helps in coordinating an effective response.
Have a clear plan in place for responding to incidents. This should include steps for containing the breach, eradicating the threat, and recovering affected systems.
- Containment Strategies: Implement strategies to contain the breach quickly to prevent further damage. This may involve isolating affected systems or networks.
- Threat Eradication: Identify and eliminate the root cause of the breach. This may involve removing malware, closing exploited vulnerabilities, or addressing insider threats.
- System Recovery: Develop and follow a recovery plan to restore affected systems to normal operations. This includes validating system integrity and ensuring data accuracy.
Cybersecurity is not a one-time effort. It requires continuous monitoring and improvement.

Conduct regular audits to ensure compliance with security policies and to identify any new vulnerabilities.
- Scheduled Audits: Conduct regular, scheduled security audits to assess the effectiveness of security measures and identify potential areas of improvement.
- Vulnerability Assessments: Perform vulnerability assessments to detect new security weaknesses. Address identified vulnerabilities promptly to maintain a strong security posture.
- Compliance Checks: Regularly check for compliance with industry standards and regulations. This helps in maintaining legal and ethical standards in cybersecurity.
Stay updated with the latest cybersecurity trends and threats. This helps in adapting your strategies to counter new threats effectively.
- Cybersecurity News and Alerts: Subscribe to cybersecurity news and alert services to stay informed about the latest threats and vulnerabilities.
- Industry Conferences and Workshops: Participate in industry conferences and workshops to learn about new technologies, trends, and best practices in cybersecurity.
- Continuous Learning: Encourage continuous learning and skill development among your cybersecurity team. This ensures they are equipped to handle emerging threats effectively.
Developing a cybersecurity framework is a critical step in protecting your organization’s information assets. By conducting a thorough threat assessment, implementing risk management strategies, establishing security policies, and preparing for incidents, you can build a strong defense against cyber threats. Remember, cybersecurity is an ongoing process that requires continuous attention and adaptation.
By following these steps, you can ensure that your organization is well-prepared to face the challenges of the digital age. Investing in a robust cybersecurity framework not only protects your assets but also strengthens your organization’s reputation and trustworthiness in the marketplace.