It started as a harmless wave of nostalgia. As 2026 dawned, the “Ten Year Challenge” evolved into the “2016 Workforce Throwback,” a social media trend encouraging professionals to post photos from a decade ago. Across LinkedIn and Instagram, feeds are flooded with images of first cubicles, decade-old conference badges, and whiteboard brainstorming sessions from the startup days of 2016.
While users see these posts as a celebration of career growth, cybersecurity experts see something far more dangerous: a treasure trove of reconnaissance data handed directly to threat actors.
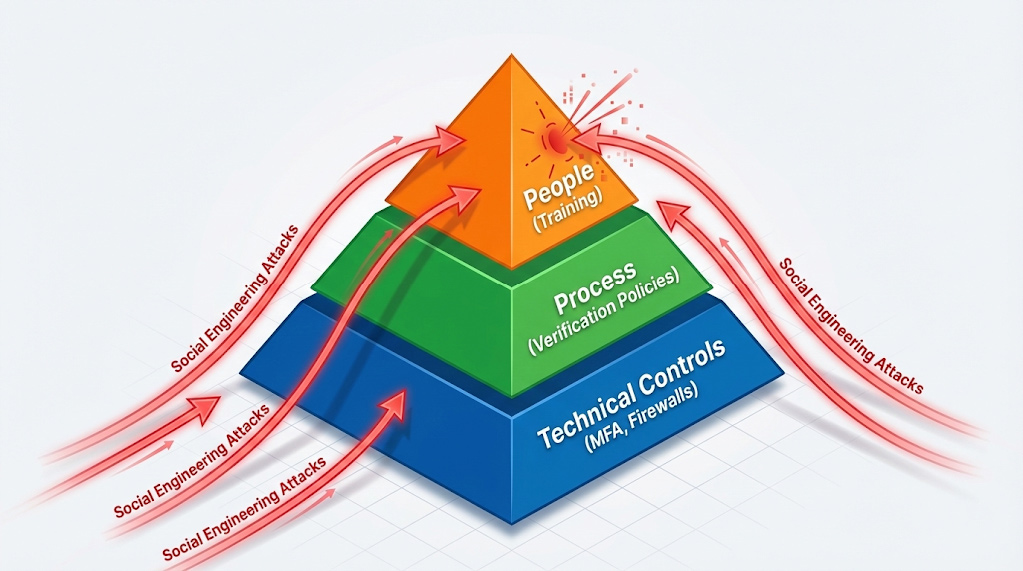
For businesses navigating mergers, acquisitions, or rapid scaling, this trend represents a significant, unquantified vulnerability. Cybersecurity strategists warn that these seemingly innocent images provide the exact context required to execute high-fidelity social engineering attacks types that bypass traditional firewalls. According to the Verizon 2025 Data Breach Investigations Report (DBIR), the human element remains a critical vulnerability, involved in approximately 68% of breaches, with pretexting and phishing leading the charge.
“The timeline of a breach often begins months before the first alert triggers,” says a senior analyst at Arann Tech. “What we are seeing now is attackers harvesting data from these viral trends to build trust profiles. They don’t need to hack your password if they can convince you to hand it over.”!
The Permanence of Reconnaissance
“There is no such thing as ‘delete’ on the internet. Every throwback post becomes permanent reconnaissance,” warns the Arann Tech strategy unit.
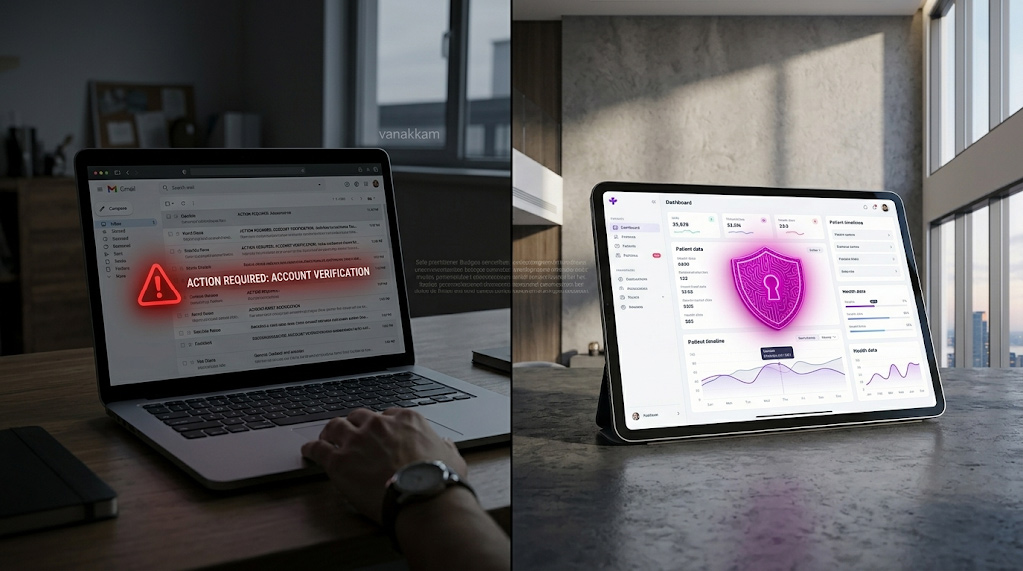
For executives and business owners, understanding what is social engineering attacks in cyber security is critical. It is not necessarily a technical exploit; it is the manipulation of human psychology to bypass technical controls. Attackers exploit trust, authority, and the natural desire to be helpful. When an employee posts a photo of their 2016 ID badge, they aren’t just sharing a memory; they are validating the visual identity of a vendor, a hierarchy, or a security protocol that may still be in use today.
The risks are not theoretical. Arann Tech has categorized the types of social engineering attacks businesses face today into four primary vectors, all of which are amplified by public data hygiene issues:
- Pretexting: This involves an attacker creating a fabricated scenario—or pretext—to steal information. By referencing details found in throwback posts (e.g., “I remember meeting you at the 2016 Sales Summit in Chicago”), attackers create a false sense of familiarity to authorize fraudulent transfers.
- Phishing: While traditional phishing casts a wide net, spear-phishing targets specific individuals. Emails referencing “your 2016 conference badge” or “the old office layout” gain instant credibility, drastically increasing the likelihood of a click.
- Baiting: Attackers leave malware-infected physical devices (like USB drives) in conspicuous places. A customized label using an employee’s pet name—gleaned from a “2016 puppy” post—makes the bait irresistible.
- Tailgating: Also known as “piggybacking,” this involves an attacker seeking entry to a restricted area. Visible office layouts in throwback photos allow attackers to map entry points and blend in with legitimate traffic.

Visual Breakdown: Anatomy of a Breach
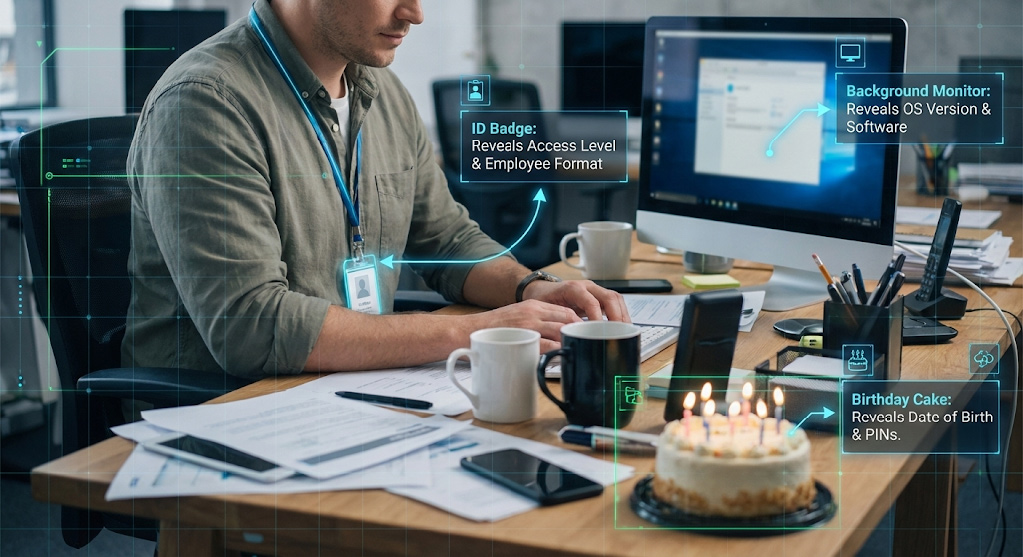
To understand what are cybersecurity risks in this context, we must analyze how attackers deconstruct a single image. Arann Tech researchers created composite examples based on real-world incident response data to illustrate how a 2016 photo translates into a 2026 breach.
Scenario A: The “First Day” Post
An employee posted a photo captioned, “Can’t believe it’s been 10 years since my first day at XYZ Corp!” The image features a smiling employee standing next to a whiteboard.
- The Risk: The whiteboard in the background, though blurry, lists client acronyms and project code names from 2016. An attacker calls the IT helpdesk today, posing as a senior vendor. They drop the legacy project code name to establish authority. “I’m working on the legacy archive for Project Apollo,” they say. The helpdesk, recognizing the valid internal code, resets a password for them.
Scenario B: The Conference Lanyard
A manager shares a picture of their lanyard from a 2016 industry expo.
- The Risk: The lanyard barcode or color-coding reveals the employee’s access level at the time (e.g., “VIP Database Admin”). LinkedIn confirms they are still with the company. The attacker now knows this target likely has elevated privileges. They initiate a password reset request, answering security questions using data found in the same social profile—such as the high school mascot mentioned in a comment thread.
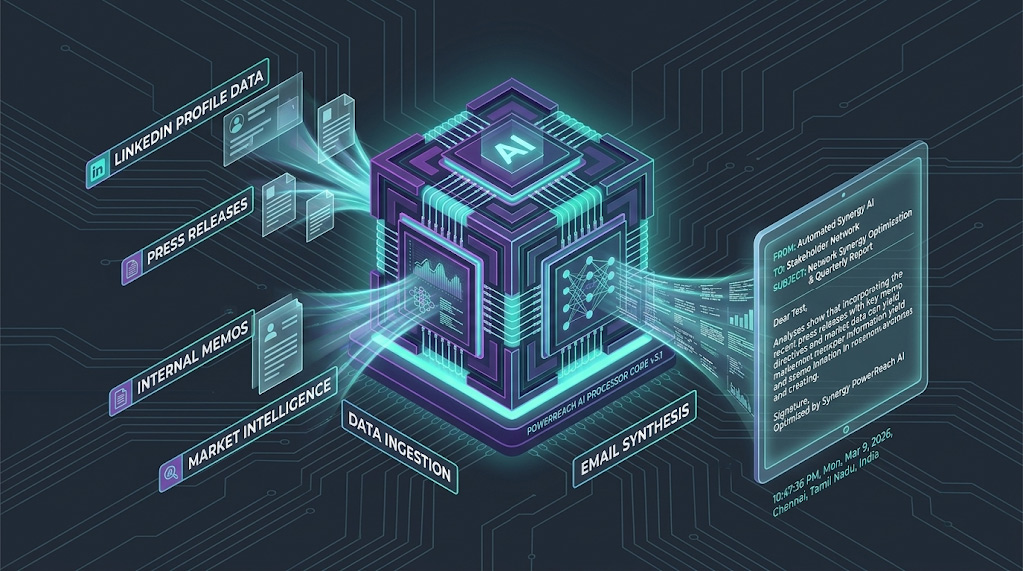
The AI Angle: Deepfake Fuel
The “Then-and-Now” format is particularly dangerous regarding cybersecurity risks involving Artificial Intelligence. By posting a 2016 photo alongside a 2026 video, users provide high-quality training data for facial recognition and age-progression algorithms. Furthermore, video clips with audio allow attackers to clone voices.
- The Threat: Attackers scrape this audio to train deepfake voice models. A finance employee receives a call from what sounds exactly like their CFO, referencing a “2016 merger” discussed in the throwback post, authorizing an urgent wire transfer.
Hidden Metadata
Many photos taken in 2016 and uploaded today still contain Exchangeable Image File Format (EXIF) data.
- The Risk: This data can reveal the exact GPS coordinates of where the photo was taken. If the photo was snapped inside a secure facility or a home office, attackers now have the physical coordinates required for dumpster diving or physical social engineering.
The Business Impact
Social engineering attacks are the number one vector for Small and Medium-sized Businesses (SMBs) because they bypass expensive firewalls by hacking the human. Recent data indicates that while large enterprises invest heavily in automated defenses, SMBs remain prime targets due to smaller security teams and reliance on legacy processes.
For a medium-sized business involved in a merger or acquisition, the stakes are existential. Attackers know that during M&A activity, email traffic is high, new vendors are being onboarded, and verify-trust procedures are often strained.
The “Throwback” trend exacerbates three specific vulnerabilities:
- Password Resets: Despite advancements in biometrics, many companies still rely on fallback security questions like “first car color,” “pet name,” or “mother’s maiden name.” These are exactly the details users share when participating in nostalgic trends.
- Vendor Impersonation: A throwback photo with a vendor’s logo creates a believable pretext. Attackers can emulate the vendor’s tone and history, making fraudulent invoices look like legitimate legacy payments.
- Physical Access: Office photos map layouts for tailgating. Knowing where the server room was in 2016 gives attackers a starting point, especially if the facility hasn’t moved.
According to IBM’s 2025 Cost of a Data Breach Report, organizations with fewer than 500 employees faced average breach costs of $3.31 million. More alarmingly, 43% of all cyberattacks target small businesses, yet many lack the continuous monitoring required to catch anomalous access patterns early.

Cybersecurity for Small Business: How to Protect Your Business
Securing your organization against social engineering requires a shift from purely technical controls to a holistic security culture. Here is a practical checklist for how to protect business assets in the age of viral trends.
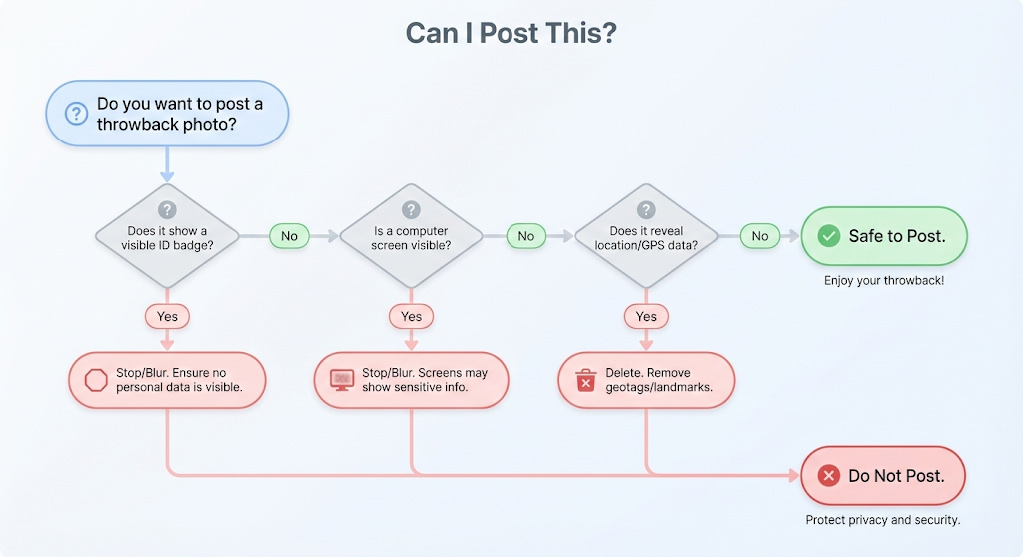
- ✅ Policy Update: Implement a clear social media policy. Explicitly prohibit “throwback” posts that feature visible ID badges, whiteboards, computer screens, or office layouts.
- ✅ Annual Archive Review: Encourage employees to review and archive old posts. What was safe to share in 2016 may be a liability in 2026.
- ✅ Escalation Training: Train staff to treat specific requests with skepticism. Adopting a mantra of “Any security question request = immediate IT escalation” can stop pretexting in its tracks.
- ✅ Technical Hardening: Replace knowledge-based authentication (security questions) with FIDO2-compliant Multi-Factor Authentication (MFA) and device trust protocols.
- ✅ Monitoring: Implement User and Entity Behavior Analytics (UEBA). If a user whose “throwback” post says they are in Chicago suddenly attempts a login from Lagos, the system should block it automatically.
Cybersecurity Risks and Controls
To understand how to mitigate cybersecurity risks, executives must map specific social engineering techniques to actionable controls.
| Social Engineering Attack Type | Business Risk | Arann Tech Control |
| Pretexting | Fake vendor emails or calls requesting payment or data. | AI-driven anomaly detection to flag unusual communication patterns or urgency. |
| Phishing | Credential harvesting via malicious links. | DMARC implementation + Continuous security awareness training. |
| Baiting | Malware infection via physical media (USB). | Endpoint behavioral analysis (EDR) to block unauthorized execution. |
| Tailgating | Physical access to server rooms or workstations. | Biometrics + Visitor AI tracking to ensure all badge-ins match authorized personnel. |
Conclusion
Social engineering attack types evolve, but human curiosity and the desire to connect remain constant. A single photo from 2016 can act as the skeleton key for a breach in 2026. While you cannot delete the internet, you can control how your organization responds to the risks it generates.
Security isn’t about stopping the nostalgia; it’s about understanding the exposure. If you are unsure where your digital footprint leaves you vulnerable, we can help you map it out.
Contact today for a conversation about your social engineering risk posture.
Disclaimer: The information provided in this article is for educational and informational purposes only and does not constitute professional legal or cybersecurity advice. While we strive to provide accurate and up-to-date information, the cybersecurity landscape changes rapidly. Arann Tech assumes no liability for any actions taken or not taken based on the information in this article. Organizations should conduct their own risk assessments and consult with qualified professionals before implementing specific security controls.
About Arann Tech: Arann Tech specializes in cybersecurity and business continuity for medium-sized businesses navigating the complexities of growth, mergers, and acquisitions.
Key Takeaways
For busy executives, here is the bottom line on the risks of the “2016 Throwback” trend:
- The Trend: Employees are posting decade-old photos of badges, office layouts, and personal milestones.
- The Threat: This data answers common security questions (e.g., “first car”) and helps attackers craft convincing impersonation scams (pretexting).
- The Stats: Social engineering drives 68% of breaches; SMBs face 43% higher costs per employee when breached.
- The Solution: Eliminate “security questions” in favor of MFA, update social media policies to ban photos of credentials, and implement continuous monitoring.
FAQs
Q: Social engineering attacks rely on which of the following?
A: They rely on human psychology—specifically attributes like trust, respect for authority, and a sense of urgency. Unlike malware that exploits software bugs, social engineering exploits human errors to bypass technical controls.
Q: What are the most common social engineering attacks types in 2026?
A: The landscape is dominated by Pretexting (often leading to Business Email Compromise), followed closely by Phishing, Baiting, and Quid Pro Quo. The rise in pretexting is linked directly to the availability of personal data from social media trends like the 2016 throwback.
Q: How can SMBs implement cybersecurity risks and controls effective against these threats?
A: SMBs must prioritize employee training combined with continuous monitoring. Annual audits are no longer sufficient. Real-time monitoring of user behavior allows businesses to detect when a compromised credential is being used, even if the password is correct.
Q: Why do throwback posts create cybersecurity risks?
A: Throwback posts provide permanent answers to security questions (e.g., “first car,” “childhood home”) and offer visual reconnaissance (badges, layouts) that attackers use to craft convincing lies.