Post-Merger Cybersecurity Integration: How to Avoid the 63% Breach Rate
Mergers spike cyber risk. In healthcare deals, breach probability doubles during the 90 days around close. Clinic leaders must act fast. This post gives a practical 90-day integration checklist with clear steps (freeze legacy admins, patch systems, monitor logs, etc.) and free AI-assisted tools. Follow this plan to safeguard patient data, avoid fines, and maintain trust.
Why Mergers Create a 90-Day Breach Window

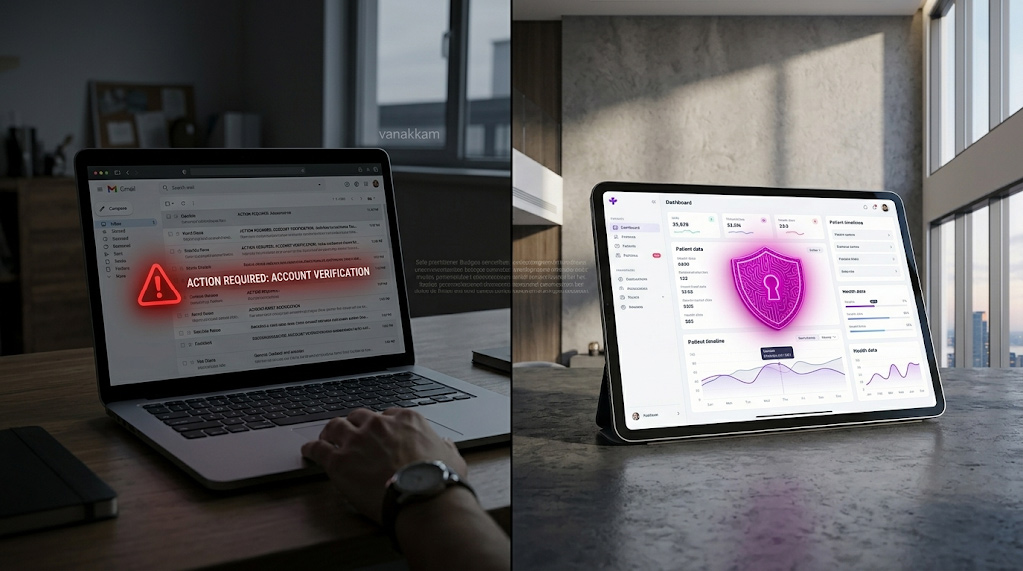
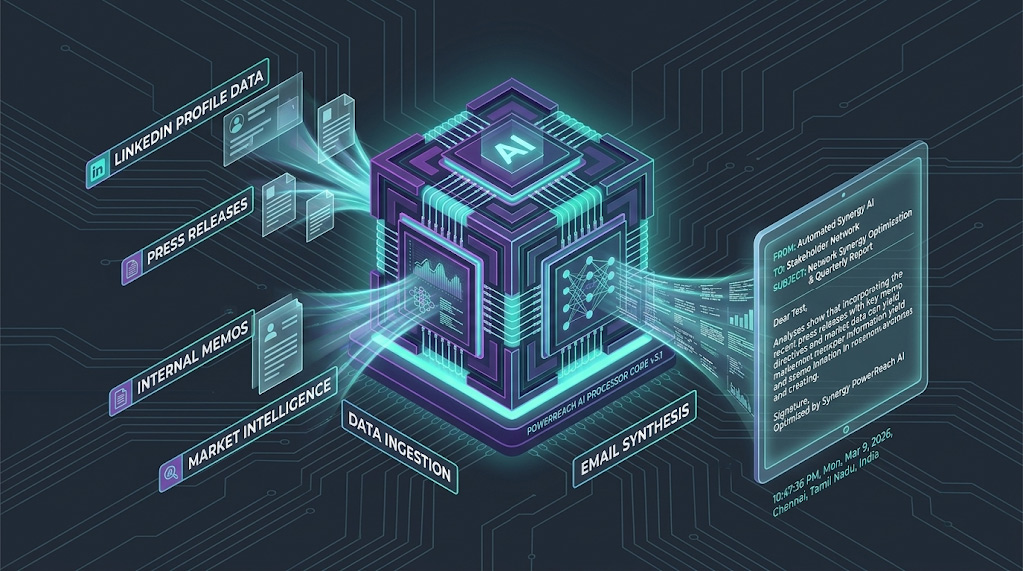
M&A deals are an open invitation to hackers. News of a merger makes both companies prime targets. Public filings and press releases leak information that reduces hackers’ uncertainty. Meanwhile, IT teams juggle systems integration, often leaving security controls untouched or inconsistent. CrowdStrike research shows attackers hide in networks an average of 95 days before being found – exactly the length of your integration window.
In short, you’re uniting two sets of credentials, devices and networks into one giant attack surface. If you delay clean-up and monitoring, adversaries lurking in either network will pounce.

Clinics and hospitals see this risk acutely. A study of health systems found that breach likelihood doubles in the year before and after a merger. When two electronic health record (EHR) systems and staff logins are combined, even a small misconfiguration can expose patient data. Every unpatched computer, orphaned user account, and forgotten security policy in the acquired clinic becomes an entry point into the parent network. This 90-day “danger zone” demands focused cybersecurity action.
The 5 Most Common Post-Merge Security Failures
Failing to plan post-close security causes the lion’s share of breaches. Here are five pitfalls (with examples and consequences) to avoid:
- Unchecked legacy admin accounts. Example: The acquired clinic has local “admin” users that nobody mentioned. After integration, those accounts still have elevated rights on the hospital network. Consequence: A thief finds one of these accounts and uses it as a backdoor to steal records and encrypt files – leading to downtime, ransom demands and HIPAA fines.
- Delayed patching of legacy systems. Example: Clinic A’s billing server uses an outdated OS. Integration is rushed, so patching is postponed. Consequence: A known vulnerability is exploited, giving an attacker easy access to the merged environment (and patient data). This can cause system outages and costly recovery operations.
- Merging networks without segmentation. Example: IT teams link the two clinic networks for email and file sharing, but forget to isolate the lab’s research network. Consequence: Malware from one segment can spread unchecked to the other, contaminating sensitive servers or disrupting critical healthcare systems.
- Incomplete identity cleanup (deprovisioning). Example: On Day 1 post-close, dozens of old user accounts (ex-staff, contractors, test users) are still active in the directory. Consequence: Stale or duplicate identities let attackers or disgruntled ex-employees access systems illegally, risking data leaks and regulatory breaches.
- No incident response plan or monitoring. Example: The merger leaves no unified SIEM or logging. The security team is caught off-guard when suspicious login spikes occur. Consequence: A breach goes undetected for weeks. By the time it’s discovered (often after patient data is leaked), the company faces massive liability, trust erosion and possible fines.
Each of these failures hits you where it hurts: patient trust, regulatory compliance (HIPAA fines can be 4–10% of revenues), and your bottom line. Recognizing them is half the battle – now let’s fix them fast.
A Practical 90-Day Post-Merger Security Playbook (step-by-step)
Below is a 5-step integration plan. Each step has sub-actions and a quick verification question to ensure completion. Treat these steps as your post-close checklist.
Step 1: Freeze and Audit All Admin Privileges. Immediately lock down and review every elevated account from both companies.
- Inventory all users with admin/root rights on servers, databases, cloud tenants, and network devices. Include local and domain admins.
- Disable or reset passwords for any redundant or no-longer-needed accounts (e.g. old service accounts, generic logins).
- Assign temporary “read-only” roles until you can vet each user.
- Verification: “Have you listed every account with full privileges and seen their last login date in the last 30 days?”
Step 2: Consolidate Identity Systems and Remove Legacy Accounts. Merge directories (AD/LDAP) securely, then purge.
- Connect directory services with strict controls (consider temporary firewall rules between networks). Do not blindly import logins.
- Identify stale accounts: filter users with no activity or missing HR data, then disable or delete them.
- Ensure multi-factor authentication (MFA) is enabled for all remote and admin accounts.
- Verification: “Are there any user accounts for former employees or unused test profiles still active?”
Step 3: Harmonize Security Policies and Patch Levels. Ensure both environments meet the same security baseline.
- Align password policies, firewall rules, and anti-malware configurations. Remove any insecure exceptions.
- Immediately apply critical patches on both sides: focus on internet-facing servers (web, email, EHR) first.
- Validate antivirus and endpoint protection agents are up-to-date and reporting correctly in both networks.
- Verification: “Can you confirm all critical systems were patched to the latest updates this week?”

Step 4: Reconnect Networks with Security Controls. Safely bridge the infrastructures for data flow.
- Use VPN/Zero-Trust and network segmentation: only allow necessary traffic (e.g. replicate EHR database, share printers).
- Perform vulnerability scanning of the combined network before going live to catch holes.
- Monitor firewall logs for unusual connections during the initial weeks of integration.
- Verification: “Are cross-network connections limited to essential services with no unknown open ports?”
Step 5: Activate 90-Day Monitoring and Incident Response. Maintain vigilance while threats surface.
- Turn on centralized logging/SIEM across both companies. Watch for anomalies like logins from strange locations or excessive data transfers.
- Schedule weekly security reviews: check user logs, vendor access, and backup integrity (ideally with immutable backups for ransomware safety).
- Finalize a clear incident response playbook covering the merged entity (roles, communications, legal notifications).
- Verification: “Is continuous 24/7 monitoring in place, and is the incident response plan updated for the new organization?”
Following these steps creates a robust integration firewall. Use this 5-step playbook as your actionable checklist to track each action and responsible owner.
Consequences: What Happens If You Ignore These Steps
Skipping thorough integration security invites disaster. Reputation and trust are on the line – a data breach post-merger can scrub years of goodwill overnight. Clinics have faced class-action lawsuits and regulatory penalties simply for having lax post-close security. In practical terms, ignoring this checklist means:
- Data theft and downtime: Patient records and intellectual property could be stolen or locked by ransomware. Recovery might take weeks, interrupting operations and costing six-figure sums.
- HIPAA and fines: A merged entity is liable for any protected health information (PHI) breaches. Regulators don’t care about acquisition status; non-compliance fines and breach notifications still apply. This can easily cost 2–5% of revenue for large breaches.
- Deal value erosion: If breaches surface later, the parent company often eats the loss. In some deals, the purchase price was reduced by tens of millions due to undetected breaches in the target.
- Legal liabilities: Post-close, the buyer is typically on the hook. Timely action is far cheaper than court judgments.
Put simply: your clinic’s data, reputation and financial health depend on proactive steps now. The good news is that a focused 90-day plan (above) neutralizes most of these threats before they materialize.

How Arann Tech Helps
Arann Tech specializes in M&A cybersecurity for healthcare. We built our own 90-day post-close framework so you don’t have to guess. Our experts guide clinic teams through identity clean-up, network hardening, and monitoring integration – all tailored for HIPAA and healthcare compliance. In short, Arann Tech lets you close your merger deal fast while we lock down security. (Join dozens of clinics we’ve secured – learn more on our M&A Cybersecurity Services page.)
FAQ
Q: What should I ask during cyber due diligence?
A: Key questions include: “Has the target experienced breaches or incidents in the past?” and “What security controls (patching, MFA, encryption) are in place?” Also ask about legacy accounts, vendor risks, and compliance history. You want to uncover any hidden compromises or gaps in the target’s security before closing. A thorough checklist helps catch risks early.
Q: How long do we need active monitoring after a merger?
A: Plan for at least 90 days of elevated monitoring. Attackers often take weeks to reveal themselves, so many experts recommend monitoring all logs and alerts continuously for 3–6 months. The first 90 days are most critical – but for added safety keep an eye out for a full year. Maintain security tools (SIEM, EDR, backups) well beyond initial integration.
Q: Who is liable if a breach happens post-merger?
A: Generally, the acquiring organization is responsible for security after closing. If patient data is exposed, regulators and courts hold the merged entity accountable, regardless of who originally owned the data. Merger agreements may include indemnities or escrow for breaches found later, but those can be hard to recover. In practice, assume liability falls on the buyer, so make security a priority.
Q: What is a compromise assessment?
A: A compromise assessment is a forensic review of the target’s environment to look for signs of hidden intrusion (suspicious logins, malware, data exfiltration). If due diligence didn’t cover this, do it before merging networks. It identifies any “time bombs” left by hackers so you can clean them out, rather than inheriting a live breach.
Q: How do we handle legacy accounts safely?
A: Treat all old accounts as high-risk. Disable or remove every user that’s not actively needed (e.g. ex-employees, duplicates, default logins). Reset passwords on shared admin accounts. Verify each remaining account has up-to-date contact info. From Day 1, use strict “least privilege” – users only get the rights they need. This prevents forgotten or orphaned accounts from being exploited.
Q: Do we need to update HIPAA compliance after merging?
A: Yes. Whenever PHI flows between entities, update your HIPAA Privacy and Security documentation. Perform a new risk analysis covering the merged IT systems. Make sure Business Associate Agreements (BAAs) are in place for any new vendors. Ensuring continuous HIPAA compliance is a must – regulators consider each merger a significant change requiring review.
Next Steps
Now is the time for action. You have a blueprint and checklist – use them. Arann Tech offers resources and help every step of the way.
Book a 15-minute risk mapping call with our experts to walk through your unique merger scenario. Or even sooner: submit your draft integration checklist to us for a FREE 12-point cyber scan (turnaround 24h). Protect your clinic’s reputation and patients today — the first 90 days are critical.
Disclaimer: This guide is for informational purposes only and does not constitute legal, financial, or technical advice. The “90-day” framework and checklists provided are generalized best practices and do not guarantee the detection of all security vulnerabilities or the prevention of data breaches. M&A transactions involve complex liabilities; “clean” technical findings do not absolve organizations of regulatory obligations under HIPAA, GDPR, or other statutes. Arann Tech assumes no liability for undetected breaches, pre-existing compromises, or penalties incurred during or after a merger integration. We strongly recommend engaging qualified legal counsel and conducting a formal Compromise Assessment before finalizing any transaction.