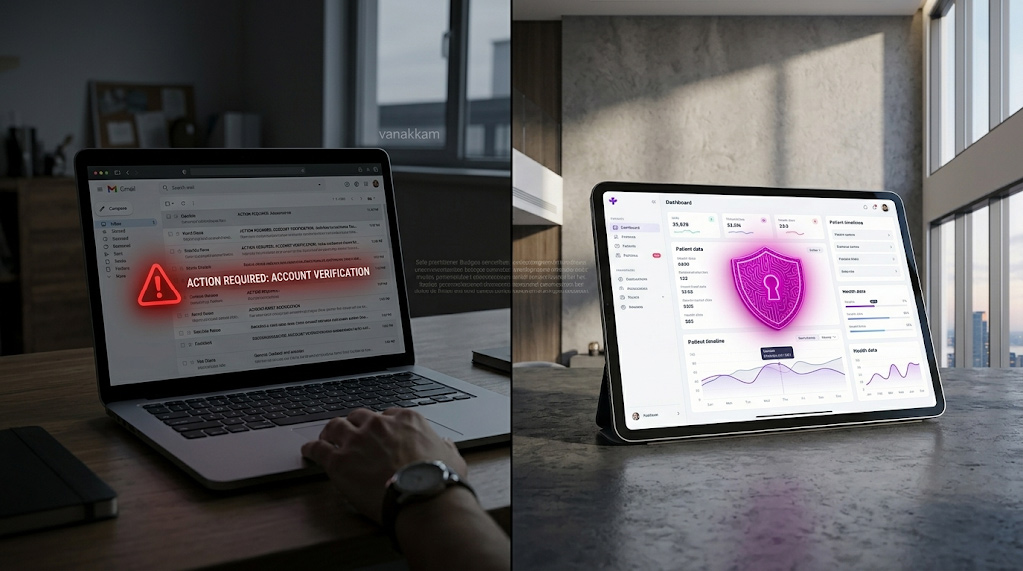
Your annual IT risk assessment passed with flying colours. The board saw a clean report. Everyone moved on.
Then the next three months happened.
Your operations team signed three new software vendors. Two senior engineers resigned. Your cloud footprint doubled overnight for a product launch. A developer set up a storage area for a weekend project and forgot to secure it.
None of that is in the audit report. And none of it is unusual. It is just how businesses operate. The question is not just what you are reviewing, but how often. And for most organisations, once a year is not enough. Your security posture is being judged against a snapshot taken months ago, while your real environment has moved on without anyone watching.
“Annual audits photograph yesterday’s risks. Quarterly assessments map today’s reality.”
This guide is for IT directors and business owners who already sense their annual review is not keeping pace, and want a practical framework for switching to a quarterly cadence without burning out their team.
How Often Should You Actually Be Reviewing Risk?
More often than most companies do, and less often than would be ideal. The goal is a cadence that catches what matters without becoming its own full-time job.
ISO 27001:2022 requires risk assessments at planned intervals and whenever significant changes occur. ISO 27001:2022 Clause 8.2 The challenge is that in a modern business, significant changes happen constantly: a new software vendor, a team restructure, a cloud migration. Each one shifts your exposure.
The structure that works for most mid-market teams is layered: lightweight automation running weekly, a quick human review monthly, a formal 90-day validation, and an annual report for the board. Each layer feeds the next.
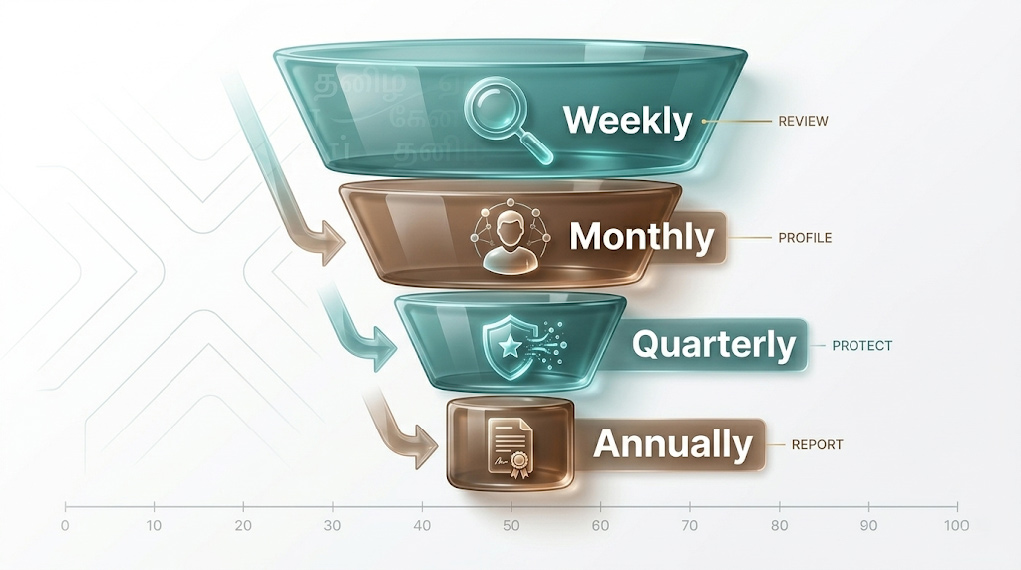
| Cadence | What You Are Doing | Why This Frequency |
| Weekly | Automated monitoring of devices and systems connecting to your environment. | Your environment changes daily. Automation catches new activity without requiring manual effort. |
| Monthly | Quick review of who has access to what, and any new software tools being used. | Accounts that should be closed and unapproved tools tend to appear between formal reviews. |
| Quarterly | Full review of controls, access, configurations, and vendor relationships. | Long enough for meaningful drift to build up. Short enough to catch it before it becomes a crisis. |
| Annually | Executive reporting and formal compliance sign-off. | Gives the board the visibility they need. Not a substitute for the operational reviews above. |
The quarterly review is the engine of this model. The weekly and monthly activities are lightweight, mostly automated, and they feed into it. What follows is how to run each layer without it consuming your calendar.
When You Cannot Wait for the Quarter
Some business events change your exposure immediately. When these happen, you need a focused review now, not at the end of the 90-day cycle.
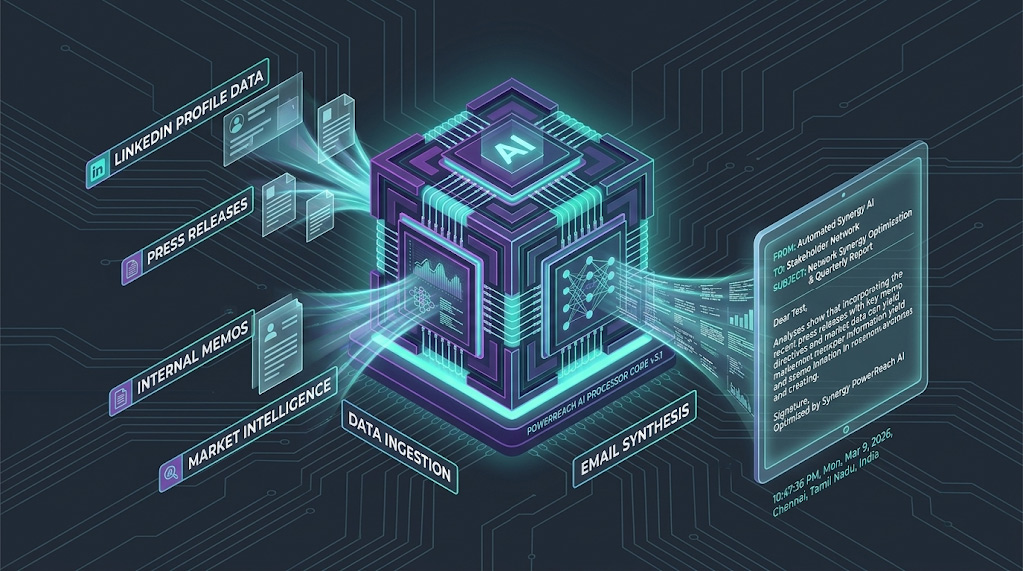
A new vendor contract
Every new software vendor is a new entry point into your business. Before they touch any data, confirm they have signed a data processing agreement, require strong authentication for their own staff, and have a documented process for handling a security incident. The depth of that review should reflect the level of data access the vendor will have. A vendor handling sensitive customer data warrants a more thorough review than one providing a standalone productivity tool. CIS Controls v8 Control 15
A senior employee departure
Removing someone from the main IT system does not automatically close every door. Staff often have access to tools managed at department level, outside the central IT team’s direct visibility. A departing employee with broad access may have active accounts in systems that are not centrally tracked. Review their access across every platform as close to their last working day as your offboarding process allows. Delays create unnecessary exposure.
A significant cloud expansion
In fast-moving businesses, new cloud environments can be set up within hours to meet a project deadline. Default settings stay in place because there is no time to configure them properly. Any meaningful expansion of your cloud footprint should trigger an immediate check that no new resources have been left open to the public internet by default.
A major software upgrade
Upgrading a core system (your finance platform, your main security tool, a critical business application) introduces a new version into your environment. New versions sometimes change what data they can access, or who can reach them, by default. After every major upgrade, verify that the new version has not quietly expanded its own access permissions.
A merger or acquisition
This is the highest-risk scenario on the list. When you acquire another company, you inherit their entire security history: their gaps, their unpatched systems, their forgotten administrator accounts. Assess the acquired environment before connecting it to your own, or as early in the integration phase as access permits. The cost of that assessment is trivial compared to the cost of inheriting an attacker’s entry point into your own business.
Why the Annual Audit Keeps Failing
Most IT leaders already know their annual review is not enough. The harder question is why organisations keep treating it as sufficient anyway. Three reasons explain most of it.

It measures the wrong day
An annual audit proves you were in good shape on one specific day. It does not prove your controls held up the day after, or three months later when your environment looked completely different. Leading security standards require that risks are continuously identified and recorded, not reviewed once a year. NIST CSF 2.0 ID.RA-01 A once-yearly snapshot cannot honestly satisfy that standard when your business changes every week.
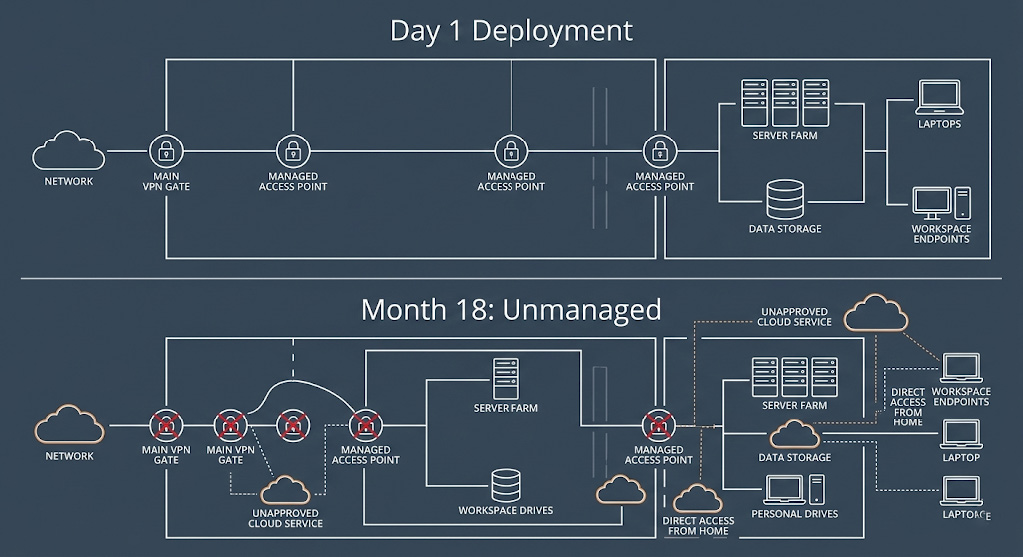
It tracks assets that no longer exist
Older risk assessments are built on static records listing physical servers and assigned laptops. Today, cloud environments can change rapidly as teams deploy new resources to meet project deadlines. You cannot protect something you do not know exists. Reviewing your full asset inventory quarterly is the minimum cadence for keeping your records close enough to reality to be useful.
It becomes a performance, not a practice
When a team knows an audit is coming once a year, preparation becomes theatre. Systems get updated in the weeks before. Evidence gets gathered retroactively. The audit passes, and the underlying gaps return within months. Quarterly reviews make this much harder, because there is no single high-stakes moment to prepare for. Good governance requires that your actual security posture reflects your real operating environment at all times, not a version tidied up for an auditor. NIST CSF 2.0 GV.OC
The 90-Day Cycle: What to Do Each Quarter
The most common objection to quarterly reviews is bandwidth. Here is the answer: you are not rebuilding the assessment from scratch. You are checking what has changed since last time. For a well-prepared team with existing documentation and tooling, the four phases below typically take two to three focused days per quarter, not a month.
Your 90-Day Review Checklist
Seven questions, one for each area that moves fastest between reviews. If the answer to any of them is unclear, that is where you start.
DAYS
1–7

Run a full sweep of every device and system connected to your environment. Compare results against the previous quarter. Anything new that was not formally approved gets investigated before it is permitted to stay. Unknown assets are not neutral. They are unreviewed risk that needs to be accounted for or removed. CIS Controls v8 Control 1
DAYS
8–14
Access and Privilege Review
Review every employee who left in the past 90 days and confirm their access has been fully removed across every system, not just the main company login. Former employees with active accounts in overlooked tools are one of the most common and preventable security exposures. While you are reviewing access, check that current team members still have only the access their role requires. Over time, accounts tend to accumulate permissions they no longer need, through promotions, project changes, or simple oversight. NIST CSF 2.0 PR.AA
DAYS
15–21
Configuration Validation
Check that any temporary access exceptions opened for project work have been properly closed. Confirm that no files or data stored in the cloud have been left open to the public internet, a common mistake during fast-paced project work. Do not overlook connected devices that sit outside the obvious IT perimeter: office printers, phone systems, and building entry systems are frequently neglected and can serve as entry points if not kept up to date. ISO 27001:2022 A.7, A.8
DAYS
22–30

Remediation and Reporting
Compile findings into a prioritised list. Assign an owner and a deadline to every item. Findings without owners do not get fixed. Build a one-page summary for your leadership team showing your current risk position, what changed since last quarter, and what decisions or resources are needed to address it. This is the document that turns security from an IT cost into a business conversation. NIST CSF 2.0 ID.RA-01
| Area | Ask This Every Quarter |
| Third-Party Risk | Have any new software vendors been added this quarter? |
| Identity and Access | Has access been removed for every person who left, across every tool they used? |
| Cloud Infrastructure | Are there any cloud services showing unexplained costs or unusual activity? |
| Patches and Updates | Have all scheduled software and security updates been completed? |
| Business Continuity | Has a backup restore test been run and confirmed working this quarter? |
| Connected Devices | Are office printers, phone systems, and building entry systems up to date and properly isolated? |
| Corporate Governance | Are any merger or acquisition integrations on track against agreed security milestones? |
Framework references: CIS Controls v8 Control 15 (Service Provider Management) · NIST CSF 2.0 ID.RA-01 (Vulnerability Identification) · NIST CSF 2.0 PR.AA (Identity and Access Control) · NIST CSF 2.0 RC.RP (Recovery Planning) · NIST CSF 2.0 GV.OC (Organisational Context) · ISO 27001:2022 Clause 8.2 (Risk Assessment) · ISO 27001:2022 Annex A.7 and A.8
Common Questions
How often should companies conduct IT risk assessments?
Most companies conduct IT risk assessments annually, but quarterly is the minimum cadence that meaningfully reflects how fast modern business environments change. ISO 27001:2022 requires assessments at planned intervals and whenever significant changes occur. ISO 27001:2022 Clause 8.2 For mid-market companies, a layered model works best: automated monitoring weekly, access spot-checks monthly, a full control validation quarterly, and executive reporting annually.
What changes require immediate IT risk assessment?
Five business events require an immediate out-of-cycle review: onboarding a new software vendor with access to company data; a senior employee departure, particularly someone with elevated system access; a significant cloud expansion or new infrastructure deployment; a major software or platform upgrade; and a merger or acquisition, which requires assessing the acquired environment before connecting it to your own.
Why do annual security audits fail modern threats?
Annual security audits fail for three reasons: they measure compliance on one specific day rather than continuously; they rely on static asset inventories that do not reflect how rapidly cloud environments change; and they create a predictable cycle that teams prepare for theatrically rather than maintaining as an ongoing practice. NIST CSF 2.0 ID.RA-01 requires that vulnerabilities are continuously identified and recorded, a standard that annual-only reviews cannot satisfy.
Quarterly Reviews Without the Overhead
The obstacle for most teams is not knowing what to do. It is finding the time to do it every 90 days on top of everything else. Arann Tech’s managed security services handle the asset discovery, access validation, and configuration checks for you. Every quarter you receive a clean executive summary and a prioritised list of what needs attention, without your team spending three weeks generating it.
Security is not a tax season event. It is a continuous part of running a resilient business.
Stop treating security like tax season.
The obstacle for most teams is not knowing what to do. It is finding the time to do it every 90 days on top of everything else.
Schedule your first quarterly assessment
Sources
1. NIST Cybersecurity Framework 2.0 (CSF 2.0). National Institute of Standards and Technology, February 2024. Available: nist.gov/cyberframework
2. CIS Controls v8. Center for Internet Security, May 2021. Available: cisecurity.org
3. ISO/IEC 27001:2022, Information Security Management Systems. Available: iso.org
This article is for general informational purposes only and does not constitute legal, regulatory, or compliance advice. Framework references are summarised for readability and should be read alongside official source documentation. Every organisation’s risk environment is different. Consult a qualified IT security professional before making decisions based on this content. Arann Tech accepts no liability for actions taken in reliance on this article.