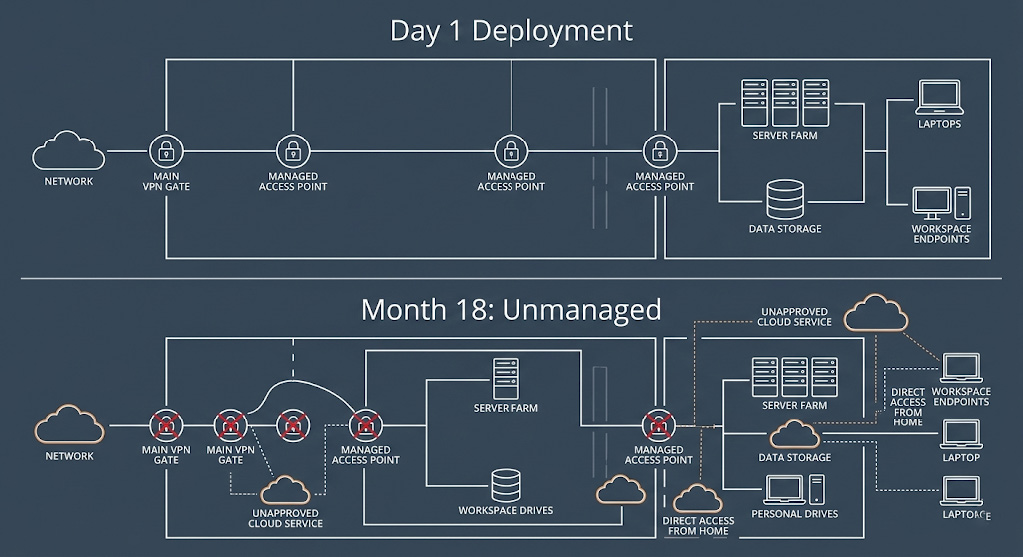
You implemented a zero trust architecture. Initially, the investment paid off. False positive alerts dropped by 40%. Remote access for your hybrid workforce finally felt secure without bottlenecking performance. The board approved the cybersecurity budget, believing the perimeter was successfully modernized. Then, operational gaps began to appear.
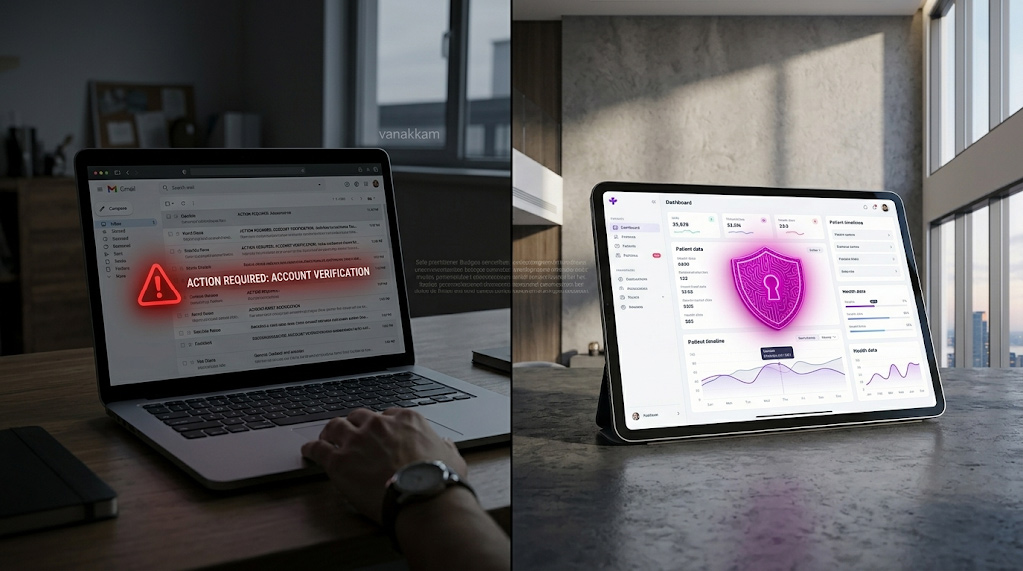
Users changed roles, but their access permissions did not update dynamically. Unpatched endpoints began bypassing compliance checks. Shadow IT created new, unmonitored data pathways. The system you built to systematically eliminate trust suddenly began trusting the wrong variables by default.
The data confirms this is the standard enterprise trajectory. According to the 2026 HPE/Cybersecurity Insiders Zero Trust Report, organizations rate their zero trust effectiveness at only 6 out of 10. The report reveals a stark gap: while 82% of organizations have committed to the framework, only 17% have achieved actual, mature ZTNA implementation. Security leaders often treat the foundational NIST SP 800-207 standard as a software product they can purchase, install, and ignore. It is not.
Zero trust security demands constant, active management. An unmanaged zero trust environment is simply an expensive, false sense of security. Here is why deployments fail over time, the core mechanics behind the philosophy, and exactly how to manage them sustainably.
What Are the Core Principles of Zero Trust Security?
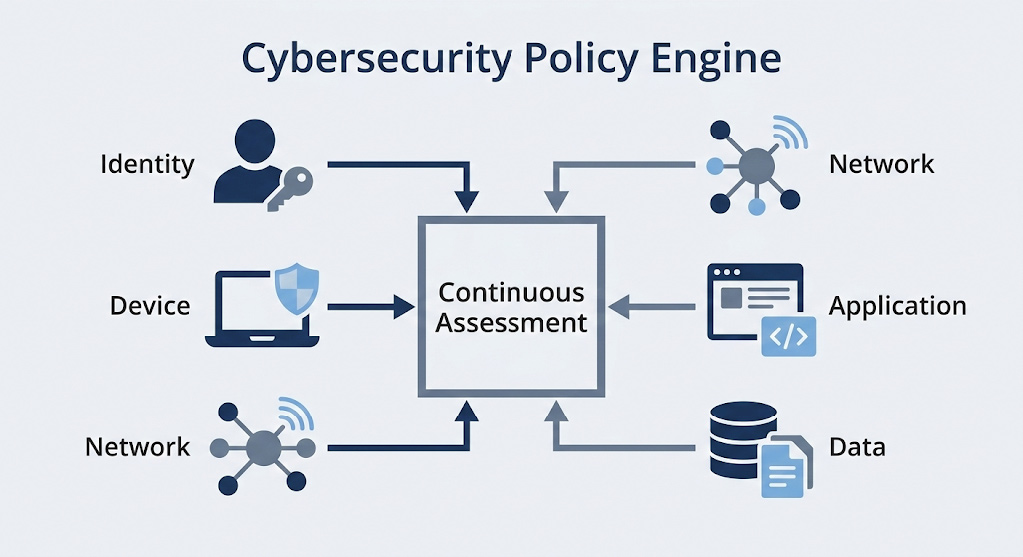
To understand why rigorous maintenance is critical, we must first define the baseline. The National Institute of Standards and Technology (NIST) established the definitive architecture blueprint in SP 800-207. True zero trust security relies entirely on the continuous enforcement of these specific foundational pillars.
Verify Explicitly Across All Vectors
Legacy networks trusted anyone or anything located inside the corporate firewall. Zero trust eliminates this inherent trust. Every single request must be explicitly verified regardless of origin. This verification checks user identity, geographic location, device health posture, and data classification. Because employee roles and device states change daily, this requires constant, active updates to identity databases to function properly.
Implement Least Privilege Access
Users and service accounts should only have access to the exact data required for their immediate task, and only for the duration of that task. This is known as Just-In-Time (JIT) and Just-Enough-Access (JEA). If a user moves from marketing to sales, their access must instantly reflect that change. Without active Identity and Access Management (IAM) oversight, least privilege quickly expands into over-privileged risk as access rights accumulate over time.
Assume Breach via Micro-Segmentation
The architecture fundamentally assumes that an attacker or compromised insider is already inside the network. To contain the blast radius of a potential compromise, the network is divided into strict micro-segments. If a threat actor compromises a single endpoint, micro-segmentation policies prevent them from moving laterally to sensitive financial databases or HR servers.
Enforce Continuous Monitoring
Initial verification at the login screen is insufficient in 2026. The system must monitor the behavior for the entire duration of the session. If an authorized user begins downloading terabytes of proprietary data at 3:00 AM – an action outside their normal behavior – the system must detect the anomaly. This requires expertly tuned User and Entity Behavior Analytics (UEBA) and Network Detection and Response (NDR) tools.
Why Zero Trust Architecture Breaks Without Management
The CISA Zero Trust Maturity Model clearly outlines the operational realities of deployment: technology alone cannot solve human organizational friction. Without a dedicated management layer, the architecture predictably experiences three specific failure modes.
Recent data underscores this exact risk. Gartner strategic planning assumptions predict that 30% of organizations will abandon zero trust initiatives by 2028, and fewer than 10% of large enterprises will reach true maturity by 2026, strictly due to operational complexity and a lack of ongoing maintenance.
Identity Drift and Stale Tokens

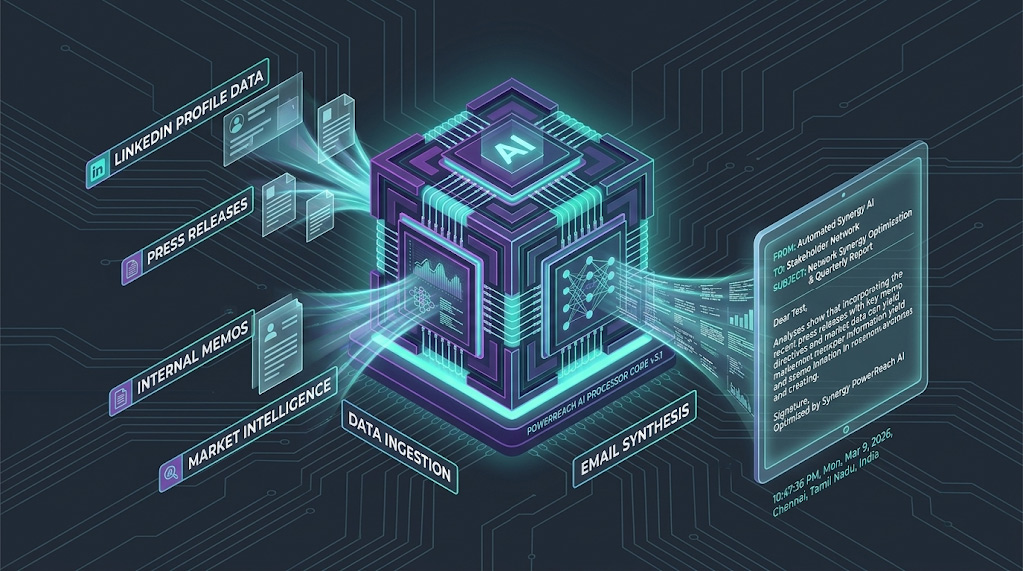
Identity drift happens when employee access rights decouple from their current job roles. A third-party contractor finishes a project, but their active directory account remains live. A mid-level manager transfers departments, retaining their old file access alongside their new permissions. Threat actors and ransomware syndicates actively hunt for these stale, over-privileged accounts. Without weekly deprovisioning audits, identity drift cripples your zero trust policy engine, allowing authorized credentials to be used for unauthorized extraction.
Device Posture Decay
Zero trust requires devices to meet strict, cryptographic health standards before connecting. This includes running the latest OS patches, having active endpoint detection (EDR), and lacking unauthorized software. However, in the real world, laptops miss update cycles. Mobile devices connect via unsecured public Wi-Fi. If your IT team is not actively managing Mobile Device Management (MDM) syncs and compliance rules, the architecture will either block legitimate executives from working or authorize compromised endpoints to access the core network.
Application Sprawl and Shadow IT
Business units adopt new SaaS applications constantly to solve immediate operational needs. If marketing spins up a new generative AI tool or cloud storage bucket that bypasses your zero trust gateways, they create massive blind spots. Shadow IT fundamentally breaks the “verify explicitly” rule. The architecture cannot protect data moving through an application API it has not been configured to see. Continuous application discovery is the only defense.
Zero Trust Network Access – The Continuous Management Layer
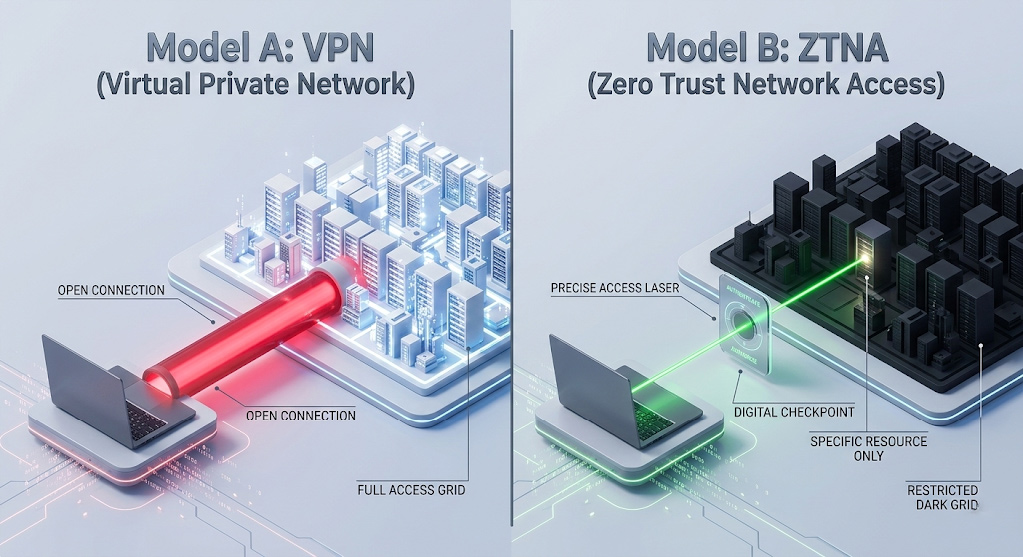
Many organizations mistakenly view Zero Trust Network Access (ZTNA) as merely a modern VPN replacement. While it does replace legacy remote access infrastructure, the underlying methodology is fundamentally different. ZTNA is the active, continuous enforcement arm of your zero trust architecture.
The VPN Lateral Movement Risk
Traditional Virtual Private Networks (VPNs) utilizing IPsec or SSL protocols grant broad, network-level access. Once a user authenticates, they are essentially placed onto the corporate LAN. They can ‘see’ servers, printers, and databases far beyond their required scope. If a hacker steals VPN credentials, they secure a highway for lateral movement. VPNs rely on static, one-time trust – a concept obsolete in the modern threat landscape.
ZTNA 1.0 vs. ZTNA 2.0 (2026 Standards)
Early ZTNA 1.0 solutions operated on an “allow and ignore” principle. They verified the user, connected them to the app, and stopped inspecting the traffic. In 2026, ZTNA 2.0 is the standard. It demands deep packet inspection and continuous security verification even after the connection is established. It inspects payloads for zero-day malware and data exfiltration attempts in real-time, requiring a highly maintained ruleset to avoid blocking legitimate business traffic.
Per-Session Dynamic Validation
ZTNA operates on continuous, dynamic validation. It connects users directly to specific applications via a secure broker, never to the underlying network itself. The applications remain hidden (dark) from the public internet.
Furthermore, ZTNA evaluates risk on a per-session basis. If an employee logs in from a corporate laptop in Toronto, the connection is approved. If that same employee attempts a massive database export 10 minutes later, the behavioral context changes. ZTNA recognizes the anomaly and terminates the session instantly.
This dynamic response requires active, expert oversight. Arann Tech’s managed ZTNA service ensures these granular policies are tuned to validate every connection accurately in real-time, preventing alert fatigue for your internal team while maintaining strict access control.
What Are the Top Zero Trust Cybersecurity Solutions Available for Enterprises?
Selecting the right underlying platform is critical, but configuring it determines your success. Based on the Gartner Magic Quadrant for Security Service Edge (SSE) and current 2026 enterprise adoption rates, four solutions lead the market in execution, scale, and completeness of vision.
Cloud-Native ZTNA Platforms
Zscaler Private Access (ZPA) remains a dominant force. It is fundamentally cloud-native, brokering connections between users and private applications without ever placing users on the network. It excels in environments strictly minimizing on-premises hardware and requires experts who understand cloud routing to manage its vast inspection capabilities at scale.
SASE and Identity Integrations
Palo Alto Prisma Access integrates ZTNA deeply within its comprehensive Secure Access Service Edge (SASE) framework. It provides robust ZTNA 2.0 threat inspection, decrypting and analyzing all traffic. Managing Palo Alto requires deep network engineering expertise to tune the advanced threat prevention blades.
Cisco Secure Access (integrated with Duo) provides an identity-first approach to networking. It leverages Duo’s dominant multi-factor authentication (MFA) footprint to enforce strict access policies based on extreme granular user trust.
Finally, the strategic combination of Okta and Netskope provides enterprise-grade IAM bundled with powerful data loss prevention (DLP) and zero trust routing, ideal for heavy SaaS users.

Which Companies Offer Zero Trust Network Access Services in Canada?
Data sovereignty is a strict, non-negotiable requirement for Canadian enterprises. Navigating compliance mandates like PIPEDA, Bill 64 (Quebec), and provincial health data laws means routing sensitive corporate data through US-based inspection nodes is often a compliance violation. Therefore, Canadian businesses require specific deployment strategies.
Global Infrastructure, Local Nodes
The major global vendors now offer localized infrastructure to solve this. Zscaler maintains dedicated, high-availability data centers in Toronto and Vancouver. Palo Alto Networks operates localized compute hubs in Calgary and Toronto. Additionally, Cloudflare One is widely available via Canadian telecommunications partners, ensuring traffic never crosses the border.
Canadian MSSPs and Mid-Market Integrators
For implementation, managed security service providers (MSSPs) bridge the gap between complex software and business reality. Large, enterprise-tier integrators like Softchoice and OnX Enterprise Solutions handle massive deployments for the public sector and enterprise space.
However, for mid-market organizations with 50 to 500 seats, bringing zero trust in-house is often cost-prohibitive. Arann Tech provides fully managed ZTNA specifically tailored for this segment. We ensure your architecture utilizes Canadian data centers exclusively. Our Zero Trust Consulting team configures the intricate routing rules, monitors the behavioral alerts 24/7, and completely manages the daily operational overhead that causes DIY deployments to fail.
The 7-Point Zero Trust Management Checklist
A sustainable architecture requires a rigid, documented operational schedule. Implement this framework to prevent the degradation associated with unmanaged environments. Rely on regular network security audits to enforce these checks and provide board-level visibility.

| Frequency | Management Task | Operational Objective & Output |
| Daily | UEBA Anomaly Review | Investigate behavioral flags (e.g., impossible travel, mass downloads) before they escalate. Output: Clean SOC incident logs. |
| Continuous | ZTNA Logging + Alerting | Ensure SIEM ingestion of all ZTNA gateway logs for real-time threat detection and correlation against endpoint data. |
| Weekly | Identity Hygiene Audit | Deprovision departed users, remove stale access tokens immediately, and enforce JIT access rules against current HR rosters. |
| Monthly | Device Posture Validation | Verify endpoint agents (EDR/MDM) are active, OS patch baselines are met, and non-compliant devices are isolated automatically. |
| Quarterly | Application Inventory Refresh | Identify Shadow IT utilizing Cloud Access Security Brokers (CASB) and integrate newly discovered SaaS apps into ZTNA access policies. |
| Bi-Annual | Zero Trust Architecture Review | Align NIST guidelines with current business workflows. Review policy engines to ensure they don’t bottleneck new remote access needs. |
| Annual | Penetration Testing | Simulate sophisticated insider threats and credential harvesting to practically verify micro-segmentation effectiveness. |
Frequently Asked Questions
What are the core principles of zero trust security?
The core principles, as defined by the definitive NIST SP 800-207 framework, include explicit verification of all users and devices, enforcing least privilege access (JIT/JEA), assuming a breach has already occurred (utilizing strict micro-segmentation), and deploying continuous monitoring to assess session risk dynamically rather than relying on a one-time login authentication.
What are the top zero trust cybersecurity solutions available for enterprises?
Based on the Gartner 2026 data for Security Service Edge (SSE) and ZTNA, the top enterprise solutions include Zscaler Private Access for scalable cloud-native delivery, Palo Alto Prisma Access for deep SASE threat inspection, Cisco Secure Access for identity-centric networking linked to Duo, and the Okta/Netskope partnership for combined IAM and data loss prevention.
Which companies offer zero trust network access services in Canada?
Canadian options include global vendors with localized, data-sovereign data centers (such as Zscaler in Toronto or Palo Alto in Calgary). Implementation and ongoing management are provided by large systems integrators like Softchoice and OnX Enterprise Solutions, as well as specialized mid-market MSSPs like Arann Tech, which provide localized, fully managed ZTNA for businesses with 50-500 employees.

Zero Trust Requires Zero Complacency
Zero Trust Architecture without constant, rigorous management is simply expensive theater. The underlying technology is highly capable of securing the modern, perimeter-less network, but it is operational discipline that actually secures the data. Do not let identity drift, shadow IT, or device decay silently compromise your critical cybersecurity investments.
If your internal IT team lacks the specialized bandwidth to manage daily ZTNA alerts, conduct weekly identity hygiene, and continuously tune micro-segmentation policies, you need a dedicated management partner.
Schedule Your Zero Trust Health Check Today
Or contact the Arann Tech advisory team directly to discuss your deployment.