Executive Summary
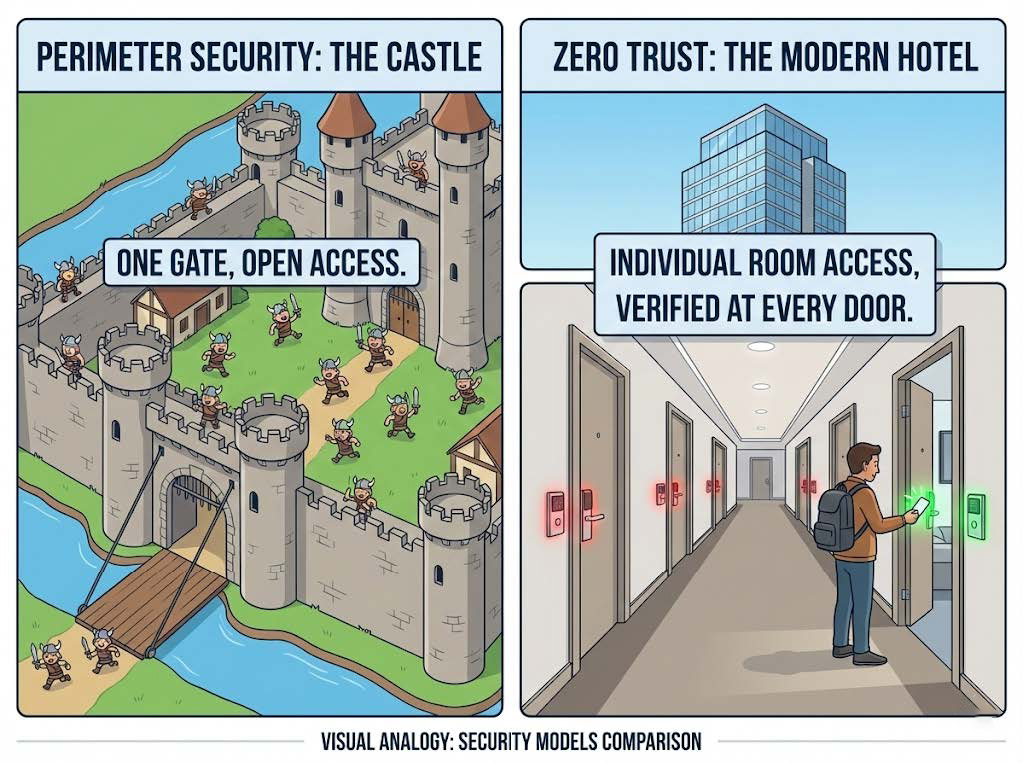
The cybersecurity paradigm that has governed enterprise defense for the last thirty years—the “castle-and-moat” perimeter model—has collapsed. For mid-market businesses, this obsolescence presents an existential crisis. Lacking the immense security budgets of the Fortune 500 but possessing data assets of equal attractiveness to cybercriminals, mid-sized organizations have become the primary targets of industrialized ransomware and extortion campaigns. The central vulnerability is no longer the firewall at the edge, but the “flat” internal network that allows adversaries, once inside, to move laterally with impunity.
This report provides a comprehensive architectural analysis of Zero Trust (ZT) as the definitive survival strategy for the mid-market. It validates the critical industry statistic that network segmentation and identity-based access controls can neutralize approximately 80% of successful cyberattacks. This figure is derived from the reality that while initial compromise is often inevitable (due to phishing or zero-day exploits), the catastrophic damage of a breach is entirely dependent on the adversary’s ability to traverse the network, harvest credentials, and locate critical assets.
By effectively implementing Zero Trust principles—specifically rigorous network segmentation—mid-market enterprises can reduce their attack surface, contain breaches to a single “blast radius,” and achieve a level of resilience that renders standard attack playbooks ineffective. This document serves as a strategic blueprint, detailing the theoretical underpinnings, technical mechanisms, and practical implementation roadmaps required to transition from implicit trust to continuous verification.
1. The Mid-Market Security Paradox: High Value, Low Friction
1.1 The Displacement of Risk to the Mid-Market

Historically, advanced persistent threats (APTs) targeted government entities and massive conglomerates. However, as large enterprises have hardened their perimeters with sophisticated EDR (Endpoint Detection and Response) and SOC (Security Operations Center) capabilities, adversaries have shifted down-market. Mid-market businesses (typically defined as 100 to 2,000 employees) occupy a dangerous “Goldilocks” zone for attackers: they possess valuable intellectual property, customer financial data, and PII (Personally Identifiable Information) comparable to larger firms, yet often rely on IT generalists rather than specialized security teams.
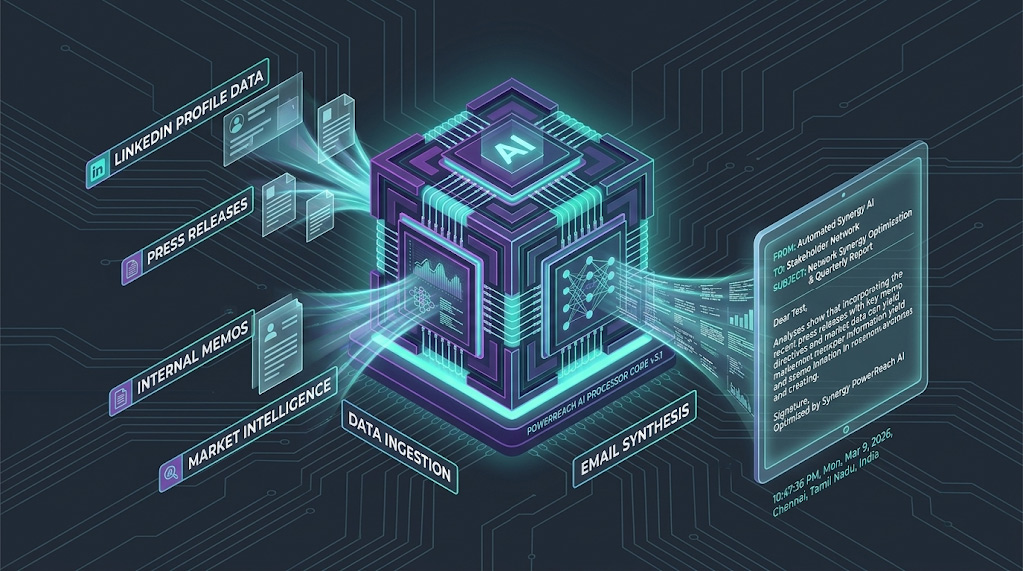
The “too small to target” myth has been definitively debunked. In 2024 and 2025, ransomware groups have increasingly automated their targeting, using AI-driven scanners to identify vulnerable edge devices regardless of the victim’s size. The industrialization of cybercrime via Ransomware-as-a-Service (RaaS) models allows affiliates to purchase access to mid-market networks from Initial Access Brokers (IABs) for as little as a few hundred dollars. The return on investment for attacking a mid-sized law firm, healthcare provider, or manufacturer is exceptionally high because these organizations are more likely to pay ransoms to avoid operational paralysis.
1.2 The Failure of Perimeter-Centric Defense
The traditional security model relies on a hard exterior shell (firewalls, VPNs) and a soft interior. This architecture operates on “implicit trust”: once a user or device clears the perimeter checks, they are trusted by default.
This model fails catastrophically in the modern threat landscape for three primary reasons:
- The Perimeter Has Dissolved: With the adoption of cloud services (SaaS, IaaS) and remote work, the “network” no longer has a distinct physical boundary. Data flows between on-premise servers, home offices, and public clouds.
- Identity is the New Vector: The majority of breaches do not involve “hacking” in the cinematic sense (breaking encryption). They involve “logging in.” Over 80% of breaches utilize lost, stolen, or weak credentials. A perimeter firewall cannot distinguish between a legitimate user and an attacker possessing that user’s valid credentials.
- East-West Traffic Blindness: Traditional security tools inspect North-South traffic (entering/leaving the network). They are often blind to East-West traffic (server-to-server or workstation-to-server). Attackers exploit this blind spot to move laterally, undetected, for weeks or months.
1.3 The Economic Impact of Flat Networks
In a flat network, where segmentation is absent, a single compromised laptop allows direct visibility and connectivity to the domain controller, backup servers, and executive workstations. This topology maximizes the “blast radius” of an attack. When ransomware strikes a flat network, it encrypts the entire environment, not just the patient-zero machine.
The cost implications are staggering. The global average cost of a data breach is projected to reach $4.44 million in 2025, but for the mid-market, the relative impact is far greater, often representing a significant percentage of annual revenue. Furthermore, cyber insurance providers now frequently mandate segmentation and Multi-Factor Authentication (MFA) as prerequisites for coverage, effectively making the “flat network” uninsurable.
2. Anatomy of the Attack: Why Segmentation is the Antidote
To understand the efficacy of Zero Trust and segmentation, one must analyze the mechanics of modern cyberattacks. The “80% reduction” statistic is grounded in the disruption of the Cyber Kill Chain, specifically the phases following initial access.
2.1 The Lateral Movement Imperative
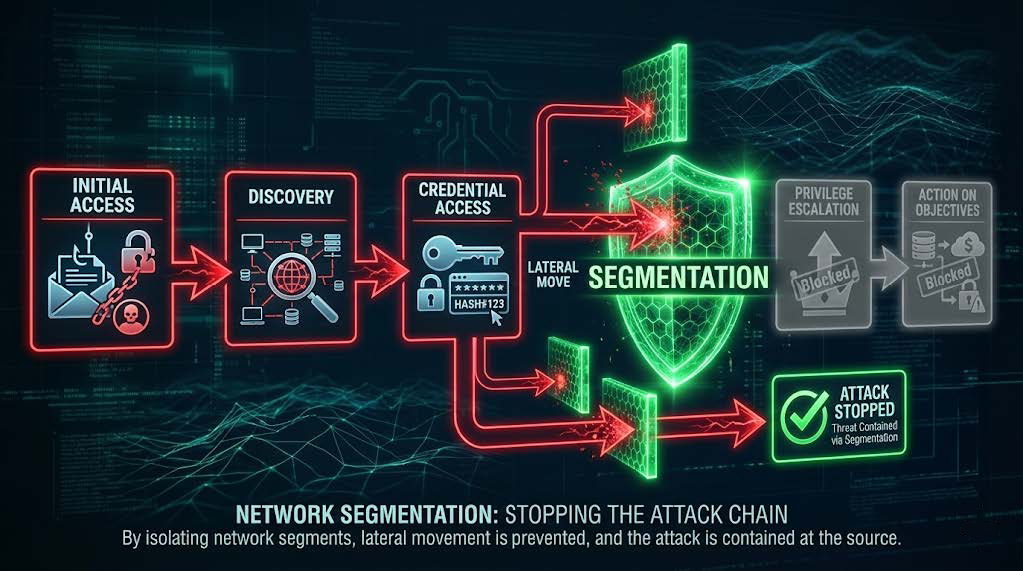
Adversaries rarely land on the target asset immediately. They land on a low-value asset—a receptionist’s workstation, a smart thermostat, or a forgotten test server—and must navigate to high-value assets. This process is known as Lateral Movement.
Table 1: The Lifecycle of Lateral Movement
| Stage | Action | Traditional Defense Response | Zero Trust / Segmentation Response |
| 1. Initial Access | Phishing email, exploited VPN vulnerability. | Perimeter firewall allows traffic if credentials are valid. | Identity verification (MFA) challenges the login; device health checks may block access. |
| 2. Discovery | Attacker scans the network (Nmap, BloodHound) to map assets and open ports. | Allowed. Internal traffic is rarely inspected or blocked. | Blocked. Workstation is in an isolated segment; cannot scan servers or other workstations. |
| 3. Credential Access | Dumping memory (Mimikatz) to find admin hashes. | Ignored. Local admin rights often allow this. | Mitigated. “Least Privilege” prevents local admin access; segmentation limits where stolen creds work. |
| 4. Lateral Move | Using RDP, SMB, or WMI to jump to a server. | Allowed. Default “Any/Any” internal rules permit connection. | Blocked. Firewall rules deny RDP/SMB from User VLAN to Server VLAN. |
| 5. Privilege Escalation | Gaining Domain Admin rights to control the network. | Allowed. Once on the DC, the attacker owns the network. | Contained. Admin interfaces are on a separate Management VLAN, inaccessible from user segments. |
| 6. Action on Objectives | Exfiltration of data; deployment of ransomware. | Too Late. Detection often happens only after encryption begins. | Prevented. Data is segmented; ransomware cannot spread beyond the initial segment. |
2.2 The “80% Statistic” Deconstructed
The assertion that network segmentation and Zero Trust controls stop 80% of attacks is supported by multiple vectors of analysis:
- Credential Abuse Mitigation: Since ~80% of breaches involve compromised credentials , limiting the scope of those credentials is the most effective countermeasure. In a segmented network, a stolen marketing user’s password does not grant access to the engineering code repository or the finance database. The credentials work, but they open an empty room.
- Disruption of “Living off the Land” (LOTL): Modern attackers use legitimate administrative tools (PowerShell, WMI, RDP) to move across the network, bypassing antivirus signature detection. This accounts for nearly 80% of current attack techniques. Segmentation blocks the network ports (135, 445, 5985) required for these tools to function between segments, effectively neutralizing LOTL tactics.
- Encrypted Threat Containment: Zscaler reports that 80% of attacks now use encrypted channels. Decrypting all internal traffic is computationally prohibitive. Segmentation funnels traffic through specific gateways where decryption can be applied selectively to high-risk flows, making detection feasible.
2.3 The Speed of Compromise
Recent data from CrowdStrike and ReliaQuest indicates that the average “breakout time”—the time it takes for an intruder to move laterally from the initial beachhead—has dropped to 48 minutes, with the fastest recorded times under one minute. Human response is too slow to intercept this. Physical (or logical) barriers must be in place before the attack to physically prevent the movement. Segmentation provides this deterministic barrier.
3. Zero Trust Architecture (ZTA): The Strategic Framework
Zero Trust is often misunderstood as a product. It is, in fact, a strategic initiative that eliminates the concept of “trusted” interfaces, IP addresses, or users. It assumes that the network is always hostile and that external and internal threats are omnipresent.
3.1 Core Principles of Zero Trust
The National Institute of Standards and Technology (NIST) Special Publication 800-207 defines the standard for ZTA. For mid-market businesses, three core tenets are paramount :
3.1.1 Verify Explicitly
Every access request must be fully authenticated, authorized, and encrypted before granting access. Verification is not a one-time event at login; it is continuous. It considers multiple attributes:
- User Identity: Is this really Alice? (MFA).
- Device Health: Is Alice’s laptop patched, encrypted, and free of malware?.
- Context: Is Alice logging in from her usual location (London) or an anomaly (Pyongyang)? Is she accessing data relevant to her role?.
3.1.2 Use Least Privilege Access
Users are granted access only to the specific resources they need, for the specific time they need them. This is the digital equivalent of “need-to-know.”
- Just-in-Time (JIT): Access is granted for a specific session and revoked afterward.
- Just-Enough-Administration (JEA): Administrators are given only the permissions required for the task (e.g., restarting a service), not full root access.
3.1.3 Assume Breach
The architecture is designed with the assumption that an attacker is already on the network. Defenses are designed to minimize the blast radius. This principle drives the requirement for network segmentation—if we assume a breach, we must build bulkheads to contain it.
3.2 The Five Pillars of Zero Trust Maturity
For a mid-market organization, ZT is implemented across five pillars. Progress in each pillar contributes to the overall security posture.
| Pillar | Description | Mid-Market Objective |
| Identity | The new perimeter. Verifying users and service accounts. | Implement MFA everywhere; consolidate directories (SSO). |
| Device | Validating the security posture of endpoints (laptops, servers, IoT). | Ensure all devices are managed (MDM) and EDR is active before access. |
| Network | Isolating resources and controlling flows. | Segmentation. Move from a flat LAN to a zoned architecture. |
| Application | Securing the workload and data processing layer. | Isolate critical apps; prevent server-to-server communication. |
| Data | Protecting the asset itself (encryption, classification). | Identify sensitive data (PCI/PII) and place it in the most secure segment. |
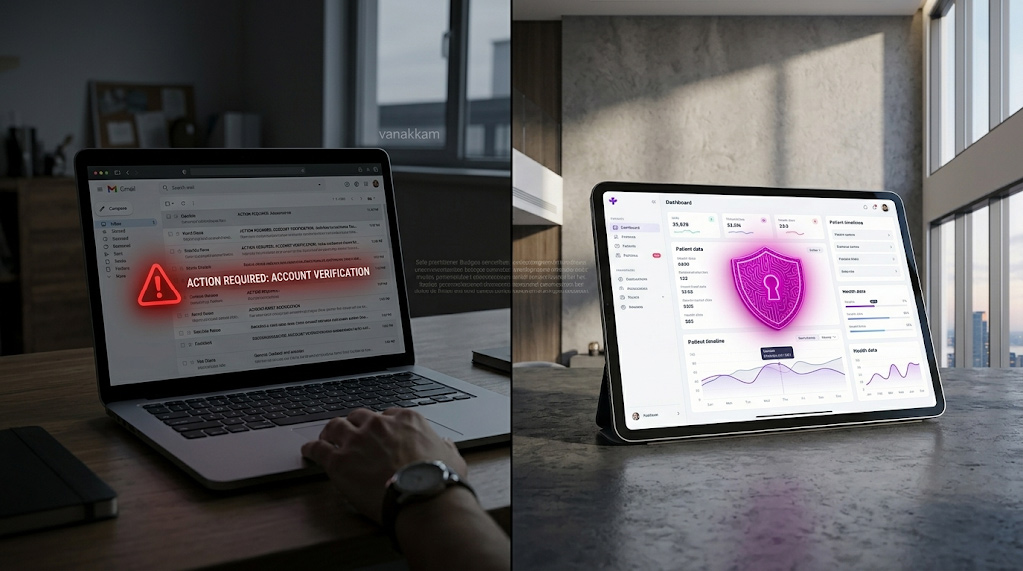
3.3 Zero Trust vs. Perimeter Security: The Hotel Analogy
To explain this shift to non-technical leadership, the “Hotel vs. Castle” analogy is highly effective.
- Perimeter Security (The Castle): Security is focused entirely on the drawbridge. Once someone crosses the moat, they have unrestricted access to the courtyard, the armory, and the royal chambers. This fails because spies (phishing) can easily steal a uniform (credentials) and walk in.
- Zero Trust (The Hotel): The hotel has a front desk (perimeter), but checking in does not grant access to the entire building. You receive a key card. That card works only for the elevator to your floor and only for your specific room door. It grants access to the gym but not the kitchen. If a criminal steals your key card, they compromise only one room, not the entire hotel. Furthermore, the electronic lock logs every entry attempt. Zero Trust turns the corporate network into a hotel where every room is locked by default.
4. Network Segmentation: The Kinetic Defense
Network segmentation is the architectural realization of the “Assume Breach” principle. It is the practice of dividing a computer network into smaller subnetworks (segments), each acting as a distinct security zone.
4.1 Types of Segmentation Technologies
Mid-market businesses often confuse different segmentation technologies. It is crucial to distinguish between physical, logical, and micro-segmentation.
4.1.1 Macro-Segmentation (VLANs)
This relies on Virtual Local Area Networks (VLANs) to logically separate devices at Layer 2 of the OSI model.
- Mechanism: Switches tag frames with a VLAN ID (e.g., VLAN 10 for HR, VLAN 20 for Engineering). Devices in different VLANs cannot communicate directly; they must pass through a router or firewall.
- Pros: Highly cost-effective; utilizes existing network switches; standard industry practice.
- Cons: VLANs alone are for organization, not security. They must be paired with Access Control Lists (ACLs) or a firewall to actually block traffic.
4.1.2 Firewall-Based Segmentation (Zoning)
This involves creating “Zones” (groups of VLANs) and routing traffic between them through a Next-Generation Firewall (NGFW).
- Mechanism: The firewall acts as the gateway for each VLAN. It applies Deep Packet Inspection (DPI), Intrusion Prevention Systems (IPS), and user-based policies to all East-West traffic crossing the zone boundaries.
- Pros: High visibility; ability to inspect traffic for malware; granular policy enforcement.
- Cons: Can become a bottleneck if the firewall is undersized; requires careful rule management.
4.1.3 Micro-Segmentation
This is the most granular form, often implemented via software agents on servers or hypervisors (e.g., VMware NSX, Illumio), rather than physical network hardware.
- Mechanism: It creates a “micro-perimeter” around every single workload or application, even if they are on the same subnet. It prevents Server A from talking to Server B in the same rack.
- Pros: Stops lateral movement completely; agnostic to physical network; aligns perfectly with Zero Trust.
- Cons: Can be complex to manage and expensive for smaller mid-market firms without dedicated staff.
4.1.4 Identity Segmentation
CrowdStrike and other vendors advocate for “Identity Segmentation,” which restricts access based on the user’s identity and risk score rather than just network IP. If a user exhibits anomalous behavior, their access to specific segments is dynamically revoked.
4.2 The “Default Deny” Posture
The critical shift in segmentation is moving from a “Default Allow” to a “Default Deny” rule set. In a flat network, the implicit rule is “Allow Any to Any.” In a segmented Zero Trust network, the final rule in the firewall policy is “Deny All.” Traffic is only permitted if it is explicitly defined as necessary for business operations.
4.3 Technical Architecture: The “Zone” Model
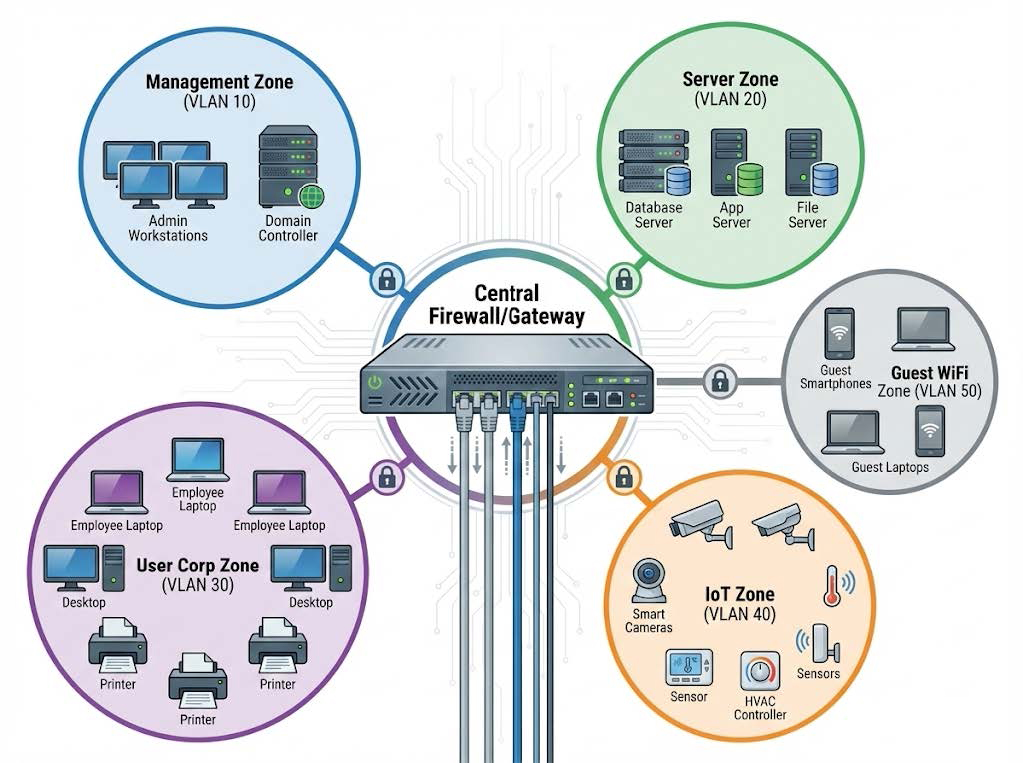
For mid-market entities, a practical architecture organizes the network into functional “Zones” with varying trust levels.
Table 2: Standard Mid-Market Zoning Schema
| Zone Name | VLAN Example | Trust Level | Description | Firewall Policy |
| Management | VLAN 10 | Critical | Network gear interfaces (switch management, firewall GUI). | Restricted to IT Admins only via Jump Host. No Internet access. |
| Servers | VLAN 20 | High | Domain Controllers, File Servers, ERP, Databases. | Inbound: Specific ports (SQL, HTTPS) only. Outbound: Patches only. |
| User Corp | VLAN 30 | Medium | Employee laptops and workstations. | Outbound Internet: Allowed (filtered). Inbound: Denied. East-West: Restricted. |
| Printers/IoT | VLAN 40 | Low | Printers, Cameras, HVAC, Smart TVs. | No Internet Access. Inbound: Print ports only. Outbound: Denied. |
| Guest WiFi | VLAN 50 | Untrusted | Visitor devices. | Internet Only. Client Isolation enabled. No access to internal zones. |
| DMZ | VLAN 99 | Isolated | Public-facing web servers. | Strictly controlled. No access to internal LAN. |
5. The “80% Statistic”: A Deep Dive into Attack Vector Mitigation
The claim that segmentation stops 80% of attacks is not marketing hyperbole; it is a statistical probability based on the reduction of available attack vectors.
5.1 Mitigation of Credential Theft (The Primary Vector)
CrowdStrike’s Global Threat Report and the Verizon DBIR consistently identify compromised credentials as the leading cause of breaches (approx. 80%).
- Scenario: An attacker steals the credentials of a mid-level HR employee via phishing.
- Flat Network Outcome: The attacker logs into the HR employee’s VPN or workstation. From there, they scan the entire network, discovering the Finance database. They use the valid HR credentials to move laterally, or exploit a vulnerability on the Finance server.
- Segmented Network Outcome: The attacker logs in. They attempt to scan the network. The firewall sees traffic from the “HR Zone” attempting to reach the “Finance Zone” on port 445 (SMB) or 3389 (RDP). The firewall checks the policy: “Does HR need RDP access to Finance?” The answer is no. The traffic is dropped. An alert is generated. The compromised credentials are useless for lateral movement.
5.2 Mitigation of Ransomware Propagation
Ransomware like Ryuk, Conti, or WannaCry often functions as a worm, automatically spreading to every device it can reach via SMB exploits (EternalBlue) or brute force.
- The Segmentation Wall: In a properly segmented network, workstations cannot talk to each other (Workstation-to-Workstation traffic is blocked). If one laptop is infected, the malware attempts to spread. It hits the segmentation barrier. It cannot reach the servers; it cannot reach other laptops. The infection is contained to a single device (n=1) rather than the entire fleet (n=all).
5.3 Mitigation of Supply Chain Risks
Third-party vendors often require access to specific systems (e.g., HVAC vendors accessing climate control, IT MSPs accessing servers).
- The Segmentation Defense: By placing vendors in a specific “Vendor Zone” or using ephemeral ZTNA access, a compromise at the vendor’s site does not grant free rein in the mid-market company’s network. The attacker riding the vendor connection is trapped in the narrow silo of access granted to that vendor.
6. Implementation Roadmap for Mid-Market Businesses
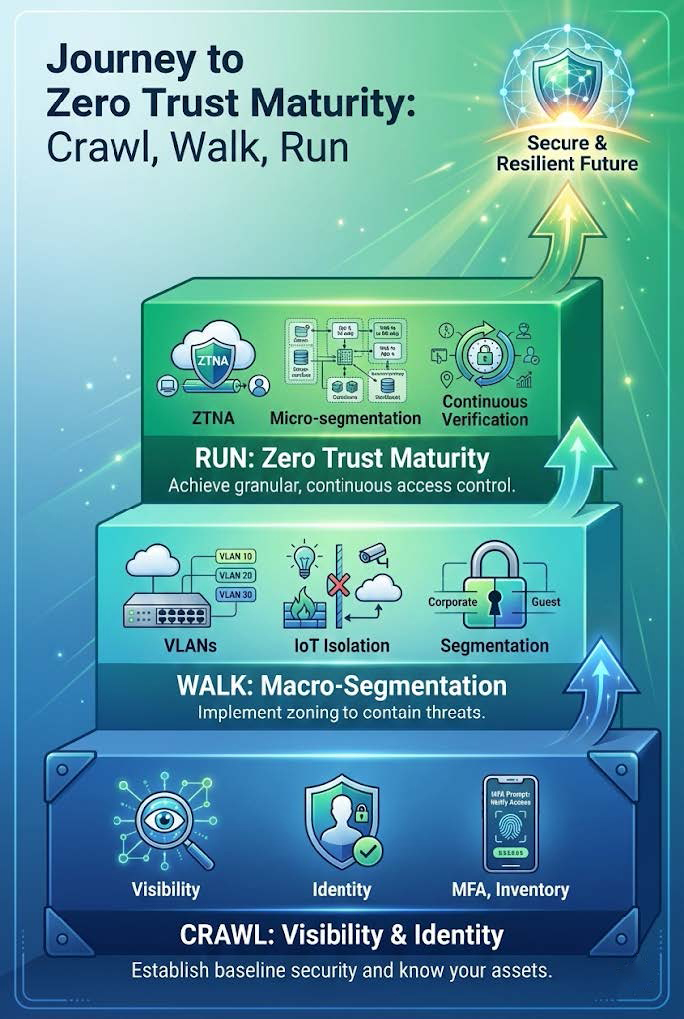
Implementing Zero Trust does not require a “rip and replace” of all infrastructure. For the mid-market, a phased “Crawl, Walk, Run” approach is the most economically viable strategy.
Phase 1: The Foundation (Months 1-2)
Focus: Visibility and Identity
- Asset Inventory: You cannot segment what you do not know. Use automated scanning tools (e.g., Lansweeper, Nmap, or firewall discovery modes) to build a complete map of all hardware, software, and data flows. Identify “Shadow IT” and unmanaged IoT devices.
- Identity Consolidation: Ensure all users are in a central directory (e.g., Active Directory or Azure AD).
- MFA Everywhere: Implement Multi-Factor Authentication for all remote access, email, and administrative logins. This is the single highest-ROI security control available.
- Guest Isolation: Immediately move Guest Wi-Fi to a separate VLAN with no routing path to the corporate network. Enable “Client Isolation” on wireless access points so guests cannot attack each other.
Phase 2: Macro-Segmentation (Months 3-6)
Focus: Protecting the Critical and the Vulnerable
- Isolate IoT and Printers: These devices are notoriously insecure and unpatchable. Move them to a dedicated VLAN. Create firewall rules that block them from initiating connections to the internal network. Allow only necessary inbound traffic (e.g., print spooler traffic from the print server).
- Server Segregation: Move servers out of the user subnet. Users and servers should not be “network neighbors.” Place servers in a dedicated “Data Center” VLAN.
- The “Default Deny” Rule: Begin building the firewall policy. Start with “Allow” rules for business-critical traffic. Once confident, switch the default rule for inter-VLAN traffic to “Block”.
Phase 3: Zero Trust Maturity (Months 6-12)
Focus: Granular Control and Automation
- User-ID Policies: Transition firewall rules from IP-based (Source: 192.168.1.50) to Identity-based (Source: UserGroup “Finance”). This ensures security follows the user regardless of their device or location.
- ZTNA Implementation: Replace the traditional VPN. VPNs extend the network perimeter to the user’s home, which is dangerous. ZTNA (Zero Trust Network Access) provides application-layer access without network-layer connectivity. If a user needs the ERP system, ZTNA proxies that specific connection without giving the user’s laptop an IP address on the internal network.
- Micro-Segmentation: If resources allow, deploy agent-based segmentation for high-value server workloads to prevent server-to-server lateral movement.
7. Technical Implementation Guide: Configuring the Defense

This section provides specific technical guidance for implementing segmentation using standard mid-market equipment (e.g., Fortinet, Palo Alto, Cisco Meraki, Ubiquiti).
7.1 VLAN Configuration (802.1Q)
Segmentation relies on the IEEE 802.1Q standard for tagging frames.
- Trunk Ports: The uplinks between switches and the firewall must be configured as “Trunks” to carry tagged traffic for multiple VLANs.
- Access Ports: The ports connecting to end-user devices (PCs, printers) are “Untagged” access ports assigned to specific VLANs.
- Routing: The firewall (or Layer 3 Core Switch) acts as the “Inter-VLAN Router.” This is the choke point where security policy is enforced. Do not use a Layer 3 switch for routing between security zones unless it supports ACLs, as switches typically route at wire speed without deep inspection.
7.2 Handling IoT: The “Taint Shared Content” Defense
IoT devices are often used as “pivots.” A compromised smart thermometer or camera can be used to scan the network.
- Step 1: Create an IoT VLAN.
- Step 2: Configure DHCP to assign IPs in a specific range (e.g., 10.10.40.x).
- Step 3: Firewall Rule: Source: IoT VLAN -> Destination: ANY -> Action: DENY.
- Step 4: Exception Rule: Source: IoT VLAN -> Destination: Vendor Cloud Update Server -> Action: ALLOW (if strictly necessary).
- Step 5: Management Rule: Source: Admin Mgmt VLAN -> Destination: IoT VLAN (Port 443/80/SSH) -> Action: ALLOW.
- Result: The IoT device is effectively air-gapped from the corporate network while still functioning.
7.3 Firewall Ruleset Best Practices
A cluttered firewall policy is a security risk. Follow this hierarchy :
- Infrastructure Rules: Allow DNS, NTP, DHCP to specific servers.
- Admin Access: Allow Management VLAN to manage devices (SSH, HTTPS).
- Business Applications: Specific allowances (e.g., User VLAN -> App Server @ TCP 443).
- Internet Access: User VLAN -> WAN (with URL Filtering and IPS enabled).
- The Cleanup Rule: ANY -> ANY -> DENY (Log enabled).
8. Compliance and Economic Justification
For mid-market leaders, the investment in Zero Trust must be justified by more than fear.
8.1 ROI and Cyber Insurance
The “Cost of Inaction” is rising. Cyber insurance premiums have increased dramatically, and coverage is often denied to organizations lacking MFA and segmentation. By implementing these controls, mid-market firms can reduce premiums and ensure insurability. Additionally, the operational cost of recovering from a contained breach (one laptop reimaged) is negligible compared to a fleet-wide ransomware event (weeks of downtime, forensic costs, legal fees).
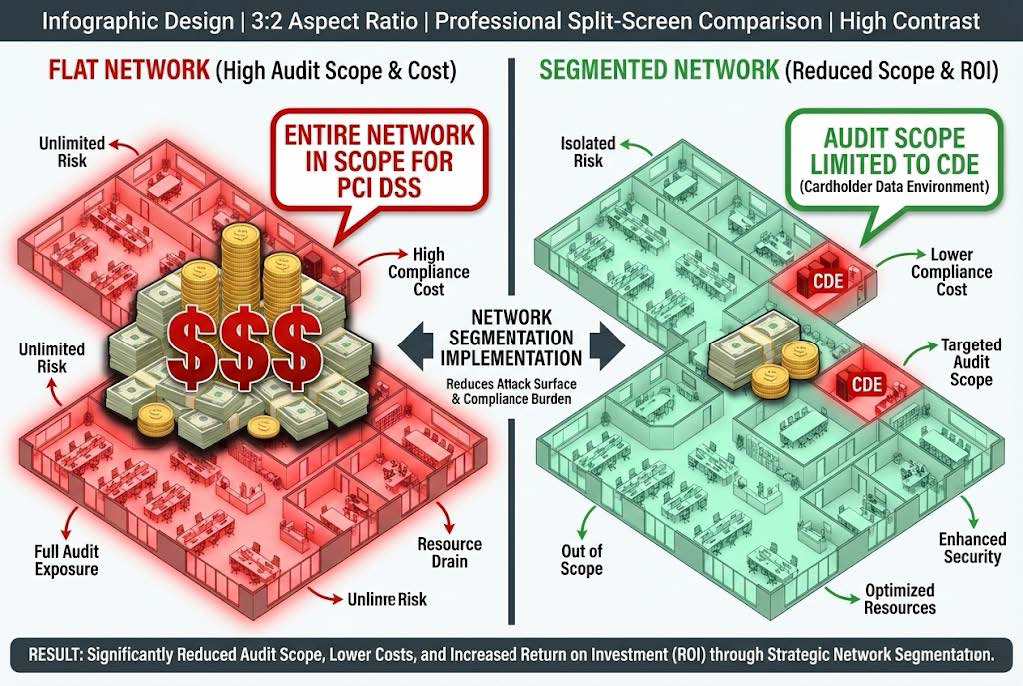
8.2 PCI DSS and Audit Scope Reduction
For retailers or businesses handling payments, segmentation is a financial strategy. PCI DSS requirements apply to the entire network segment where card data is processed.
- Flat Network: The entire company is “in scope.” Every cashier, camera, and back-office PC must meet stringent PCI standards.
- Segmented Network: Only the Cardholder Data Environment (CDE) VLAN is in scope. This drastically reduces the cost, time, and complexity of annual audits.
8.3 Operational Efficiency
Contrary to the belief that security slows down operations, segmentation improves network performance. By breaking up large “broadcast domains,” network noise (broadcast storms) is contained within a single VLAN. This reduces congestion for latency-sensitive applications like VoIP and video conferencing, resulting in a better user experience.
9. Future Trends and the Evolution of Trust

The threat landscape is not static. Mid-market architectures must evolve to meet emerging threats.
9.1 AI-Driven Threats vs. Segmentation
Artificial Intelligence is allowing attackers to generate sophisticated phishing campaigns and adaptive malware at scale. While AI helps attackers bypass detection (EDR/Antivirus), it cannot bypass a hard network segmentation rule. If the “wire is cut” logically between HR and Engineering, AI-driven malware cannot bridge that gap. Segmentation remains a “physics-based” defense that is resilient to AI sophistication.
9.2 Non-Human Identities (NHI)
As automation grows, the number of “Non-Human Identities” (Service Accounts, API Keys, Bots) is exploding—outnumbering human users 50:1 in some environments. Zero Trust principles must be applied to these entities. Service accounts should not have domain admin rights; they should be restricted to specific VLANs and ports, just like human users.
10. Conclusion
For the mid-market enterprise, Zero Trust Architecture is not a luxury; it is the prerequisite for digital survival. The data is unequivocal: reliance on the perimeter is a failed strategy. By shifting the focus from “keeping them out” to “stopping them from moving,” businesses can neutralize the vast majority of modern cyberattacks.
The implementation of network segmentation, underpinned by robust identity verification, dismantles the adversary’s playbook. It turns the network from a wide-open field into a labyrinth of locked doors. While the journey requires effort—mapping assets, defining policies, and managing change—the destination is an organization that is resilient, compliant, and unyielding in the face of the inevitable breach. The “80% reduction” is not just a statistic; it is the difference between a minor IT incident and a business-ending catastrophe.