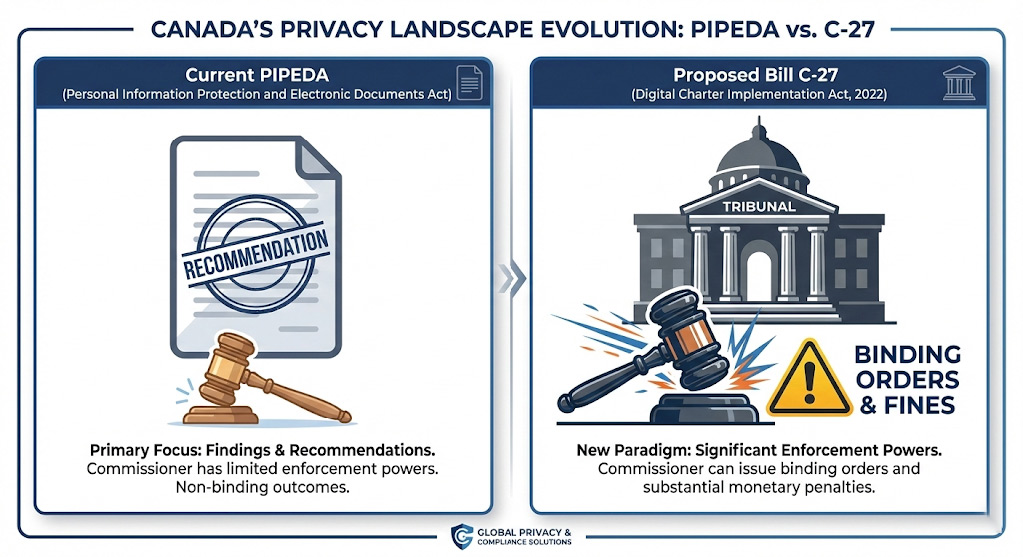
For more than two decades, the Canadian private sector has operated under the Personal Information Protection and Electronic Documents Act (PIPEDA). Enacted in the early days of the digital revolution, PIPEDA was designed as a “light-touch” framework, aiming to balance the individual’s right to privacy with the legitimate needs of organizations to collect, use, and disclose personal information for commercial purposes.
Its hallmark was the ombudsman model, a system where the Privacy Commissioner of Canada (OPC) served as an investigator and advocate, armed with the power of persuasion, recommendation, and public reporting, but notably lacking the authority to impose binding orders or substantial financial penalties directly.
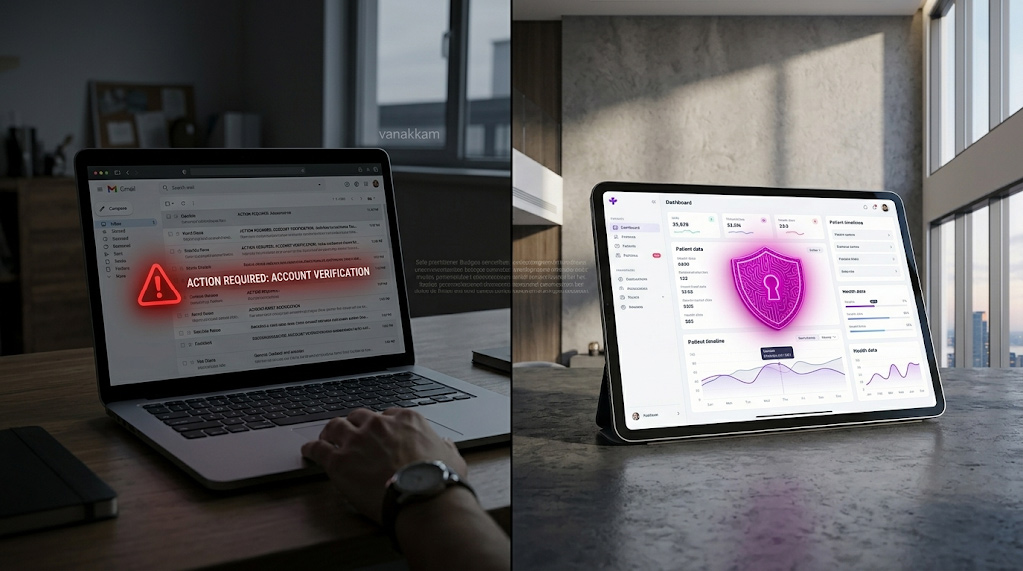
This era of “soft compliance,” where the primary risks of non-compliance were reputational damage or the arduous but non-punitive process of Federal Court applications, is rapidly drawing to a close. The introduction of the Digital Charter Implementation Act, 2022 (Bill C-27) signals a fundamental philosophy shift in Canadian privacy law. Although Bill C-27 has faced legislative hurdles most notably dying on the Order Paper in January 2025 due to the prorogation of Parliament its provisions represent the unequivocal direction of federal policy: a move toward a regime of hard enforcement, heavy financial consequences, and rigorous accountability.
For Canadian business owners, CFOs, and IT Directors, understanding this shift is not an academic exercise in legal theory; it is a critical component of risk management. The proposed legislation seeks to repeal Part 1 of PIPEDA and replace it with the Consumer Privacy Protection Act (CPPA), alongside the Artificial Intelligence and Data Act (AIDA) and the Personal Information and Data Protection Tribunal Act (PIDPTA). If enacted, this suite of laws will align privacy law in Canada with the stringent standards of the European Union’s General Data Protection Regulation (GDPR) and Quebec’s Law 25, introducing administrative monetary penalties (AMPs) that could reach the greater of $25 million or 5% of global gross revenue for the most egregious offences.
This article provides an exhaustive analysis of how these proposed changes will impact your current PIPEDA compliance posture. We will dissect the text of the proposed bill, contrast it with existing obligations, and provide a detailed operational roadmap for mid-market and enterprise organizations. The thesis here is simple: while the principles of privacy remain consistent, the cost of failure is about to increase exponentially.
Section 1: What Is Actually Changing Under Bill C-27?
To fully appreciate the operational impact of Bill C-27, one must first understand the structural limitations of the current law and why the federal government views reform as an economic imperative. PIPEDA is often criticized by privacy advocates as a “tiger with no teeth.” While it established a global standard for fair information practices in 2000, its enforcement mechanisms have failed to keep pace with the data-driven economy.
Currently, if the Privacy Commissioner finds that an organization has mishandled personal data, they can issue a report with non-binding recommendations. If the organization refuses to comply, the Commissioner (or the complainant) must apply to the Federal Court for a hearing de novo, essentially starting the legal process from scratch. There are no administrative fines for substantive violations like collecting data without consent; fines exist only for specific technical breaches, such as failing to report a data breach, and these require criminal prosecution.
Bill C-27 proposes to dismantle this ombudsman model and replace it with an adjudicative and enforcement-driven framework. This represents a profound transformation in Canadian data privacy law, reallocating the burden of risk from the individual to the enterprise.
The New Enforcement Architecture: Commissioner and Tribunal
The proposed CPPA introduces a bifurcated enforcement structure designed to ensure both investigative rigor and procedural fairness, addressing long-standing criticisms of the singular ombudsman role.
The Privacy Commissioner’s Enhanced Powers (Order-Making)
Under the proposed CPPA, the Privacy Commissioner of Canada transitions from an advisor to a regulator with teeth. The bill proposes granting the Commissioner the power to conduct inquiries and, upon finding a contravention, issue binding compliance orders.
Specific powers proposed under this new authority include:
- Cessation Orders: The Commissioner could order an organization to stop collecting, using, or disclosing personal information immediately if it is done in contravention of the Act.
- Compliance Measures: The Commissioner could order an organization to implement specific measures to comply with the Act, such as rewriting privacy policies, implementing specific security safeguards, or altering data retention practices.
This “order-making power” means that the regulator’s decision has the force of law. Ignoring a Commissioner’s order would not trigger a negotiation; it would constitute a separate, severe violation of the Act. For IT Directors, this means that a finding of inadequate security is no longer a “recommendation” to upgrade firewalls—it is a legal mandate to do so.
The Personal Information and Data Protection Tribunal
Perhaps the most significant structural innovation in Bill C-27 is the creation of the Personal Information and Data Protection Tribunal. This specialized administrative body would serve as the arbiter of penalties and appeals.
Currently, appeals of Commissioner findings go to the Federal Court. The proposed Tribunal is designed to be a more agile, specialized body comprising members with expertise in information and privacy law. Its role is twofold:
- Imposing Penalties: While the Privacy Commissioner can recommend a financial penalty following an inquiry, they cannot impose it. The Tribunal is the body authorized to review the Commissioner’s recommendation and formally impose the penalty.
- Hearing Appeals: Organizations that disagree with a Commissioner’s finding or order can appeal to the Tribunal. The Tribunal’s decisions are final and binding, subject only to judicial review by the Federal Court on limited grounds.
Section 2: The Three Biggest Operational Impacts for Mid-Market Companies
While the threat of fines garners attention, the true cost of Bill C-27 lies in the operational friction it introduces. Compliance is no longer a passive state of “not misusing data”; it requires active, technically complex capabilities to fulfill new individual rights. For mid-market companies and enterprises, three specific areas represent the highest hurdles between current operations and proposed compliance.
1. Proposed Private Right of Action
Under the current PIPEDA regime, individuals have limited direct recourse against organizations. While they can file a complaint with the OPC, they generally cannot sue an organization for a statutory privacy violation unless the Commissioner issues a report and the individual subsequently applies to the Federal Court for a hearing—a process that is time-consuming, costly, and rarely utilized by average consumers.
The Change: Statutory Liability
Section 107 of the proposed CPPA introduces a statutory Private Right of Action. This provision allows individuals to sue an organization for damages for loss or injury suffered as a result of a contravention of the Act.
The Conditions: A “Gatekeeper” Model
Crucially, this right is not an immediate “open season” for litigation. The proposed legislation includes a gatekeeping mechanism designed to prevent frivolous lawsuits while enabling legitimate claims. An individual can only commence an action if:
- The Privacy Commissioner has made a finding that the organization contravened the CPPA; or
- The Tribunal has upheld such a finding on appeal.
Once this finding is established, the path to civil litigation is cleared. This effectively turns the Privacy Commissioner’s regulatory findings into a “pre-packaged” liability verdict for class-action lawyers. If the regulator finds you at fault, the heavy lifting of proving liability is largely done; the litigation then focuses primarily on the quantum of damages.
2. Expanded Right to Deletion (Disposal)
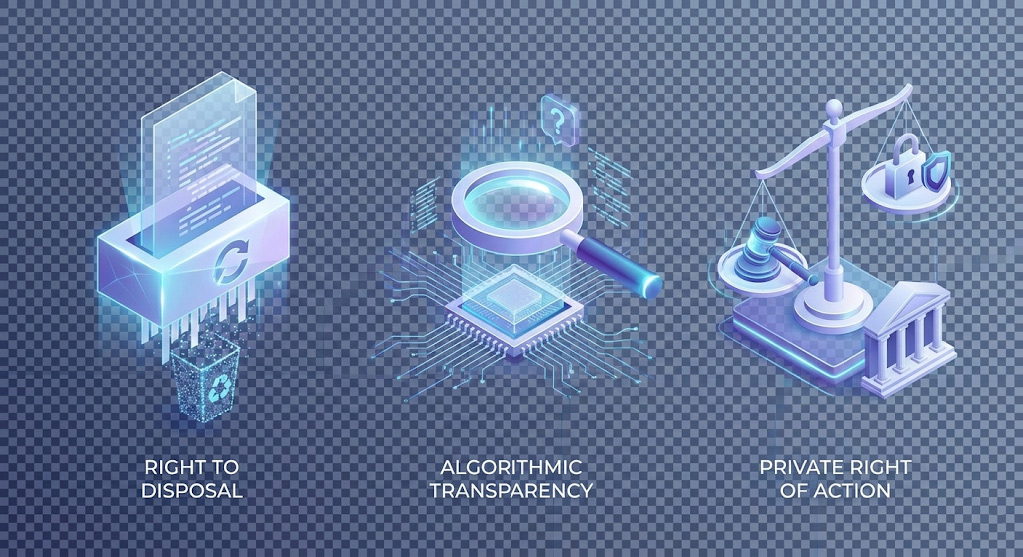
Current PIPEDA principles require organizations to destroy, erase, or make anonymous personal information that is “no longer required to fulfill the identified purposes.” This is primarily a data retention principle, governed by the organization’s own policies and schedules.
The Change: Consumer-Driven Deletion
Section 55 of the proposed CPPA introduces an explicit Right to Disposal. It allows individuals to request the permanent deletion of their personal information held by an organization, subject to specific exceptions (such as where retention is required by law or reasonable business necessity).
The “Irreversible” Standard
The definition of disposal in the proposed bill is stringent: “permanent and irreversible deletion.” This poses massive technical challenges for IT Directors in mid-market infrastructure:
- Backups and Archives: Most enterprise disaster recovery systems are designed to be immutable or at least difficult to modify to prevent data corruption. Deleting a single customer’s record from a linear tape file or a rigid cloud snapshot is often technically impossible without destroying the entire backup set or re-hydrating the data.
- Data Lakes and Warehouses: In complex enterprise environments, data is often replicated across development, testing, staging, and analytics environments. “Irreversible deletion” requires a data inventory maturity that few Canadian companies currently possess. If a customer asks to be deleted, do you know every S3 bucket, SQL table, and CSV export where their name appears?
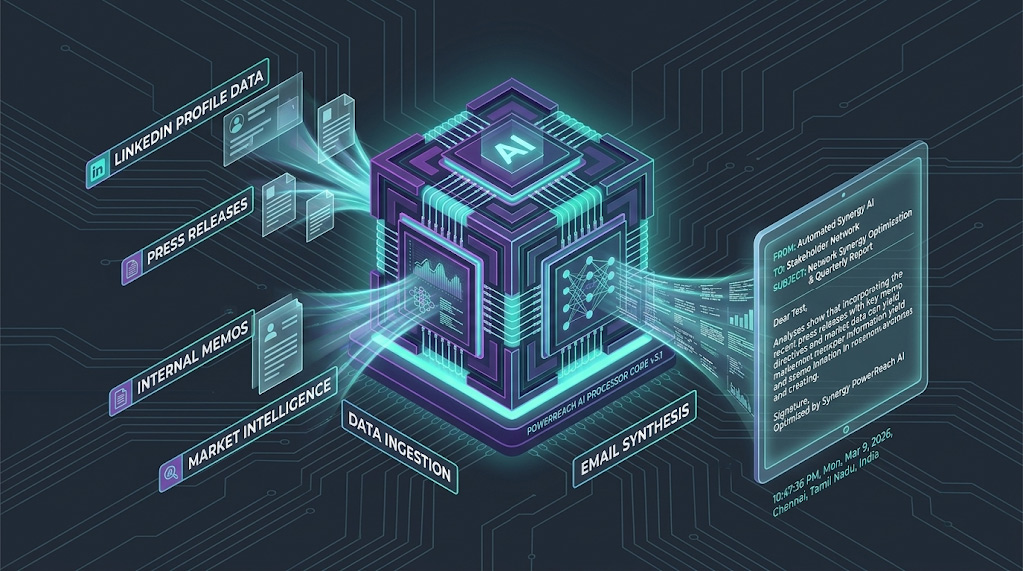
3. Algorithmic Transparency (AIDA – High-Level Only)
Bill C-27 is unique in that it bundles privacy reform (CPPA) with AI regulation (AIDA). While AIDA is technically a separate act within the bill, its impact on privacy compliance is inseparable for companies using automated decision-making.
The Change: Explaining the “Black Box”
The CPPA itself (distinct from AIDA) proposes amendments that require transparency for Automated Decision Systems. If an organization uses an automated system to make a prediction, recommendation, or decision about an individual that could have a “significant impact” on them, the organization must provide an explanation of the prediction, recommendation, or decision upon request.
AIDA’s Role (High-Level)
The Artificial Intelligence and Data Act (AIDA) applies specifically to “high-impact” AI systems. While “high-impact” is to be defined fully in future regulations, companion documents suggest it includes systems used for:
- Screening services: Determining access to credit, housing, or insurance.
- Employment: Using algorithms to rank resumes or evaluate employee performance.
- Biometrics: Identification systems using facial recognition or voiceprints.
Section 3: PIPEDA vs. CPPA (Comparison Table)
To visualize the shift from the current soft-law framework to the proposed hard-law regime, the following comparison highlights the critical divergences across key compliance areas.
| Area | PIPEDA (Current Law) | CPPA (Proposed Bill C-27) |
| Enforcement Model | Ombudsman (Recommendations & Reports) | Adjudicative (Orders & Tribunal) |
| Fines (AMPs) | None for privacy violations (only technical breach reporting). | Up to 3% of global revenue or $10M. |
| Criminal Offences | Limited (breach recording failures). | Up to 5% of global revenue or $25M. |
| Consent | Implied consent widely used; complex guidelines. | Express consent reinforced; new “Legitimate Interest” exception. |
| Individual Rights | Access and Correction. | Access, Correction, Disposal (Deletion), Mobility. |
| Privacy Management | “Accountability” principle (Schedule 1). | Mandatory Privacy Management Program (Statutory). |
| Private Right of Action | Limited (requires Federal Court application). | Statutory right following a finding of contravention. |
Deep Dive: The Evolution of Consent
Under PIPEDA, implied consent has been a flexible tool for businesses. The CPPA proposes to tighten this by explicitly defining what constitutes valid consent, requiring that information be provided in “plain language” that the target audience can understand. However, it also introduces a pragmatic pressure valve: the Legitimate Interest exception.
This exception allows organizations to collect or use personal information without consent if it is for an activity in which the organization has a legitimate interest that outweighs any potential adverse effect on the individual.
- The Opportunity: This aligns Canada with the GDPR and reduces “click fatigue.” It means businesses might not need explicit consent for fraud detection, network security, or basic product improvement.
- The Governance Burden: To rely on this, an organization must conduct a Privacy Impact Assessment (PIA) to prove that the “legitimate interest” outweighs the user’s privacy loss. This introduces a paperwork burden: you can’t just claim legitimate interest; you must document the balancing test beforehand.
Section 4: What Does Not Change
Amidst the anxiety of “proposed fines” and “tribunals,” it is vital for Canadian business owners to recognize the continuity in the system. Bill C-27 is an evolution, not a total revolution, of the fundamental principles of Canadian privacy law.
Core Privacy Principles Remain Intact
PIPEDA is built on ten fair information principles (Accountability, Consent, Limiting Collection, Limiting Use, Disclosure and Retention, Accuracy, Safeguards, Openness, Individual Access, and Challenging Compliance). The CPPA codifies these principles directly into the text of the law rather than referencing them as a schedule, but the core logic remains identical. If your organization is genuinely compliant with PIPEDA today—meaning you practice data minimization, purpose limitation, and transparency—you are already 80% of the way to CPPA compliance.
Not All Companies Will Face Maximum Penalties
While the maximum penalties are eye-watering ($25M), the expected enforcement direction is proportionate. Privacy regulators in Canada typically reserve maximum fines for organizations that demonstrate negligence, willful misconduct, repeated systemic failures, or obstruction of justice. A mid-market company that suffers a breach despite having a robust Privacy Management Program and cooperating with the regulator is unlikely to face the statutory maximum. The CPPA explicitly lists factors for determining penalties, including the organization’s efforts to mitigate harm and its history of compliance.
Enforcement is Expected to be Risk-Based and Phased
Historically, Canadian regulators have adopted a “compliance first” approach. Even with new powers, it is expected that the Office of the Privacy Commissioner will focus its limited resources on high-risk sectors (finance, health, tech platforms) and systemic issues. Small businesses acting in good faith will likely face education and compliance orders before crushing financial penalties.
Section 5: 90-Day Practical Readiness Checklist (Actionable)
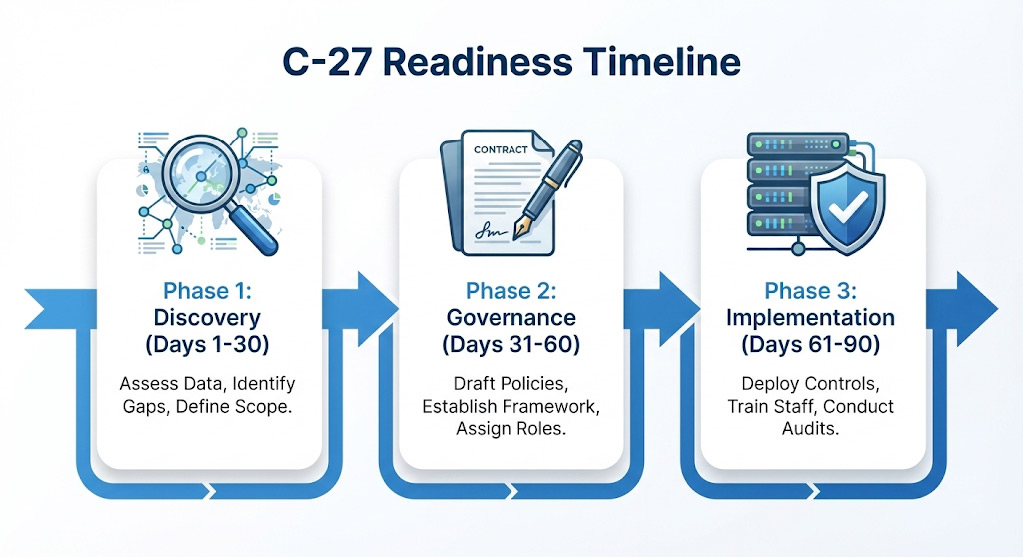
While Bill C-27 is not yet active law (and as of January 2025, died on the Order Paper due to prorogation), the operational capabilities it demands cannot be built overnight. Prudent organizations are treating the text of C-27 as the “standard to beat.” Waiting for Royal Assent is a strategy for non-compliance, as implementation of these technical controls often takes 12-18 months.
Phase 1: Assessment & Discovery (Days 1-30)
- Map All Personal Data Flows: You cannot govern what you cannot see. Conduct a comprehensive data inventory. Where does customer data enter? Where is it stored (including “shadow IT,” local spreadsheets, and third-party SaaS)? Where does it leave? Create a Record of Processing Activities (ROPA).
- Identify Data Retention vs. Deletion Gaps: Assess your current retention schedules. Do you have a “delete” button that works? Compare your technical ability to delete data against the proposed “permanent and irreversible” standard.
- Review the “High-Impact” AI Inventory: Identify any automated systems making decisions about employment, credit, or service access. Determine if your vendors can provide the “plain language” explanations required by the proposed legislation.
Phase 2: Governance & Contracts (Days 31-60)
- Review Vendor and Processor Contracts: The CPPA places heavy emphasis on the transfer of data to service providers. Review contracts to ensure vendors are contractually obligated to assist with data deletion requests, provide transparency for AI, and report breaches within strict timelines.
- Rewrite Privacy Policies in Plain Language: Move away from legalistic jargon. The proposed law requires that information be provided in language that the target audience can reasonably understand.
- Develop the Privacy Management Program (PMP): Draft the internal policies required by Section 9 of the CPPA. This includes training materials for staff, complaint handling procedures, and the specific roles responsible for privacy.
Phase 3: Technical Implementation & Testing (Days 61-90)
- Test Data Deletion and Access Request Workflows: Conduct a tabletop exercise. If a customer demanded the deletion of all their data today, could you execute it across your CRM, email backups, and third-party marketing tools within 30 days?
- Breach Response Simulation: The CPPA proposes strict reporting requirements. Test your incident response plan. Can you determine “real risk of significant harm” (RROSH) within hours of a breach?
- Front-Line Training: Train customer service staff on the new rights. If a customer asks, “Why did the algorithm reject my application?”, staff must know that this is a potential legal transparency request, not just a customer service complaint.
Conclusion
The transition from PIPEDA to the framework proposed in Bill C-27 represents the maturation of Canadian privacy law. For businesses, it signals the end of the “notice and consent” era and the beginning of the “accountability and enforcement” era.
While the bill’s legislative path has been paused, the direction of travel is undeniable. The combination of Tribunal-backed fines, a statutory private right of action, and stringent disposal rights creates a trifecta of risk that cannot be managed by a privacy policy update alone. It requires deep operational changes to how data is stored, managed, and governed.
The companies that succeed under this new regime will be those that stop viewing privacy as a legal hurdle and start treating it as a core component of their data infrastructure. The cost of preparation today is a fraction of the cost of enforcement tomorrow.
Don’t wait for enforcement actions or litigation risk to define your compliance posture.
Download Arann Tech’s Bill C-27 Readiness Audit Checklist Arann Tech: Bill C-27 Readiness Audit Checklist
Disclaimer: The content provided in this report is for informational purposes only and does not constitute legal advice. The status of legislation (Bill C-27) is subject to change, and organizations should consult with legal counsel for specific compliance obligations.
FAQ Section
What is PIPEDA compliance?
What is PIPEDA compliance? It refers to adhering to the Personal Information Protection and Electronic Documents Act, Canada’s current federal private-sector privacy law. Compliance requires organizations to obtain meaningful consent for the collection, use, and disclosure of personal information; to limit collection to what is necessary; to safeguard data with appropriate security measures; and to be accountable for data under their control.
When will Bill C-27 take effect?
As of January 2025, Bill C-27 has technically “died on the Order Paper” due to the prorogation of Parliament. It is not currently active law. However, because it represents the government’s long-term strategy to update privacy laws and maintain “adequacy” status with the EU (GDPR), similar legislation is expected to be reintroduced by a future government. Businesses should view the C-27 proposals as the inevitable blueprint for future compliance standards and prepare accordingly.
Does PIPEDA apply to employee data in Canada?
Generally, no—with a major exception. PIPEDA currently applies to employee data only for federally regulated works, undertakings, and businesses (FWUBs), such as banks, airlines, telecommunications companies, and interprovincial transportation. For the vast majority of businesses (retail, manufacturing, services) that are provincially regulated, employee privacy is governed by provincial laws (in BC, Alberta, Quebec) or common law/employment law, not PIPEDA.